Long description
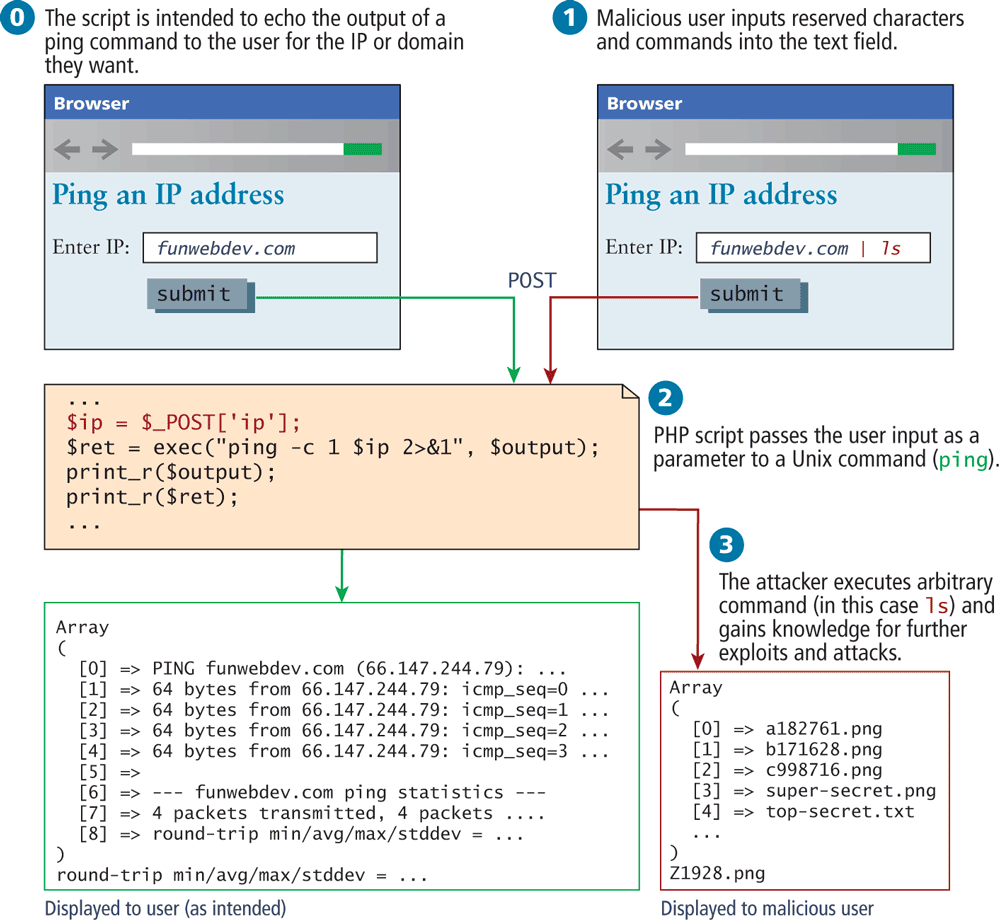
Two browsing windows are shown at the top. Browser 1: The browser contains one level-1 heading and form content. The following is labeled above the browser: The script is intended to echo the output of a ping command to the user for the I P or domain they want. The browser starts with a level 1 heading that reads Ping an IP address. Next is a form content that reads from top to bottom as follows: Enter IP colon and text box. The text box has funwebdev dot com. Next is a button labeled submit.
Browser 2: The browser contains one level-1 heading and form content. The following is displayed above the second browser: malicious user inputs reserved characters and commands into the text feild.The browser starts with a level 1 heading that reads Ping an IP address. Next is a form content that reads from top to bottom as follows: Enter IP colon and text box. The text box has funwebdev dot com pipe ls. Next is a button labeled submit.
PHP code block reads :
Line 1: dollar ip equals dollar underscore POST open square bracket apostrophe ip apostrophe close square bracket semi colon at indentation level 0. Line 2: dollar ret equals exec open bracket open double quotes ping hyphen c 1 dollar ip 2 close angle bracket ampersand 1 close double quotes comma dollar output close bracket semi colon at indentation level 0. Line 3: print underscore r open bracket dollar output close bracket semi colon at indentation level 0. Line 4: print_r open bracket dollar ret close bracket semi colon at indentation level 0.
Text box for Array 1 reads:
Line 1: Array at indentation level 0. Line 2: open bracket at indentation level 0. Line 3: open square bracket 0 close square bracket right double arrow PING funwebdev dot com open bracket 66 dot 147 dot 244 dot 79 close bracket colon at indentation level 1. Line 4: open square bracket 1 close square bracket right double arrow 64 bytes from 66 dot 147 dot 244 dot 79 colon icmp underscore seq equals 0 at indentation level 1. Line 5: open square bracket 2 close square bracket right double arrow 64 bytes from 66 dot 147 dot 244 dot 79 colon icmp underscore seq equals 1 at indentation level 1. Line 6: open square bracket 3 close square bracket right double arrow 64 bytes from 66 dot 147 dot 244 dot 79 colon icmp underscore seq equals 2 at indentation level 2. Line 7: open square bracket 4 close square bracket right double arrow 64 bytes from 66 dot 147 dot 244 dot 79 colon icmp underscore seq equals 2 at indentation level 2. Line 8: open square bracket 5 close square bracket right double arrow. Line 9: open square bracket 6 close square bracket right double arrow hyphen hyphen hyphen funwebdev dot com ping statistics dash dash dash at indentation level 1. Line 10: open square bracket 7 close square bracket right double arrow 4 packets transmitted, 4 packets at indentation level 1. Line 11: open square bracket 8 close square bracket right double arrow round hyphen trip min forward slash avg forward slash max forward slash stddev equals at indentation level 1. Line 12: close bracket at indentation level 0. Line 13: round hyphen trip min forward slash avg forward slash max forward slash stddev equals at indentation level 0.
Text box for Array 2 reads:
Line 1: Array at indentation level 0. Line 2: open bracket at indentation level 0. Line 3: open square bracket 0 close square bracket right double arrow a 182761 dot png at indentation level 2. Line 4: open square bracket 1 close square bracket right double arrow b 171628 dot png at indentation level 1. Line 5: open square bracket 2 close square bracket right double arrow c 998716 dot png at indentation level 1. Line 6: open square bracket 3 close square bracket right double arrow super hyphen secret dot png at indentation level 1. Line 7: open square bracket 4 close square bracket right double arrow top hyphen secret dot txt at indentation level 1. Line 8: dots at indentation level 1. Line 9: close bracket at indentation level 0.
There is a text after array that reads Z 1928 dot png at indentation level 0.
Steps to exploit of a command-line pass-through of user input.
Step 0: The script is intended to echo the output of a ping command to the user for the IP or domain they want. Text appears on top of Browser 1
Step 1: Malicious user inputs reserved characters and commands into the text field. Text appears on top of Browser 2
Step 2: PHP script passes the user input as a parameter to a Unix command open bracket ping close bracket. In normal case, Array 1 text is Displayed to user open bracket as intended close bracket.
Step 3: The attacker executes arbitrary command open bracket in this case 1s close bracket and gains knowledge for further exploits and attacks. Array 2 text is Displayed to malicious user.
Back