Long description
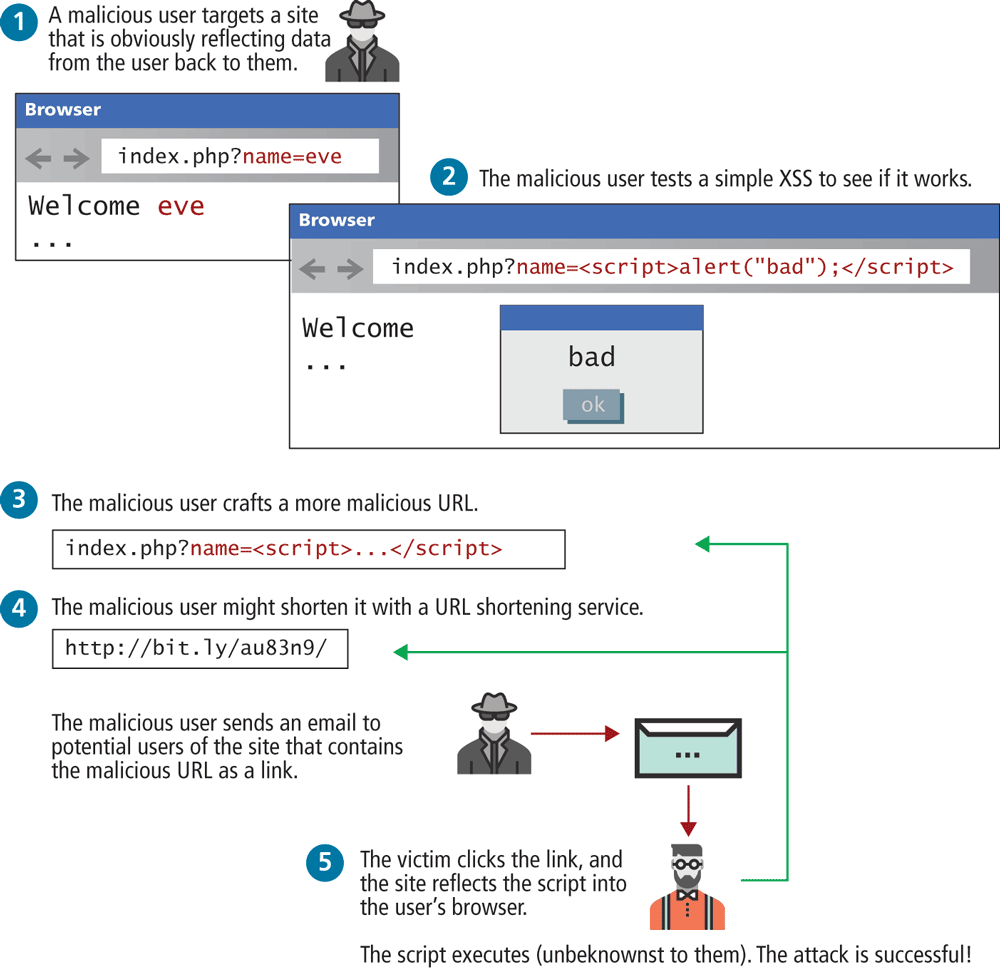
Two browser windows are shown in the image. The different steps to be followed for the Reflection X S S attack are also shown below.
Browser 1: The address text bar reads index dot p h p question mark name equals eve. Welcome eve displayed on the page.
Browser 2: The address text bar reads index dot php question mark name equals open angle bracket script close angle bracket alert open bracket open double quotes bad close double quotes close bracket semi colon open angle bracket forward slash script close angle bracket. Welcome and popup window with content bad and ok button displayed on the page.
Various steps illustrating Reflect X S S attack is as follows.
Step 1: A malicious user targets a site that is obviously reflecting data from the user back to them. Text shown above Browser 1.
Step 2: The malicious user tests a simple X S S to see if it works. Text shown above Browser 2.
Step 3: The malicious user crafts a more malicious URL. Code reads index dot php question mark name equals open angle bracket script close angle bracket dots open angle bracket forward slash script close angle bracket
The malicious user might shorten it with a URL shortening service. Code reads http colon forward slash forward slash bit dot l y forward slash a u 8 3 n 9 forward slash
Step 4: The malicious user sends an email to potential users of the site that contains the malicious URL as a link.
Step 5: The victim clicks the link, and the site reflects the script into the user's browser.
The script executes open angle bracket unbeknownst to them close angle bracket. The attack is successful exclamation mark
Back