Long description
Two browsing pages are shown on top of the image.
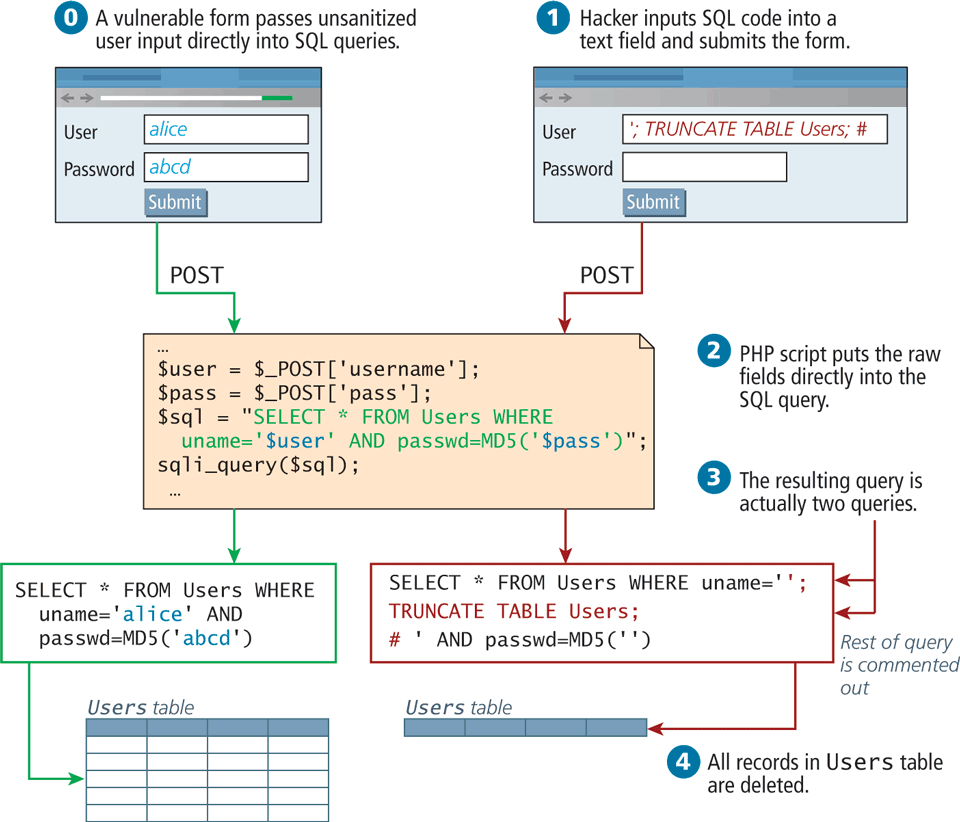
Browser 1: On top of this browser the following is labeled: A vulnerable form passes unwanted user input directly into S Q L queries. The browser starts with a form content. The content top to bottom are as follows: User and text box. The text box corresponding to user is labeled alice. The bottom textbox is labeled "a" b c d. Below this shows a submit button. The output from Browser 1 is POST to P H P code.
Browser 2: The browser starts with a form content as follows: Hacker inputs S Q l code into a text field and submits the form. The content top to bottom are as follows: User and text box. Text box is labeled semi colon TRUNCATE TABLE Users semi colon hash. Below this , Password and an empty text box placed side by side. Next is a button labeled Submit. The output from Browser 2 is POST to PHP code.
P h p code block reads as follows.
Line 1: dollar user equals dollar underscore POST open square bracket apostrophe username apostrophe close square bracket semi colon at indentation level 0. Line 2: dollar pass equals dollar underscore POST open square bracket apostrophe pass apostrophe close square bracket semi colon at indentation level 0.
Line 3: dollar sql equals open double quotes SELECT asterisk FROM Users WHERE at indentation level 0. Line 4: uname equals apostrophe dollar user apostrophe AND passwd equals M D 5 open bracket apostrophe dollar pass apostrophe close bracket end double quotes semi colon at indentation level 1. Line 5: s q l i underscore query open bracket dollar s q l close bracket semi colon at indentation level 0. The output from PHP code block feed into 2 SQL queries.
SQL code 1: SELECT asterisk FROM Users WHERE uname equals start quote alice end quote AND passwd equals MD5 open bracket apostrophe a b c d apostrophe close bracket.
SQL code 2: SELECT asterisk FROM Users WHERE uname equals double quotes semi colon TRUNCATE TABLE Users semi colon hash quote AND passwd equals MD5 open bracket double quotes close bracket
The steps for SQL injection attack open bracket right close bracket and intended usage open bracket left close bracket.
Step 0: A vulnerable form passes unsanitized user input directly into SQL queries. This is text above Browser 1
Step 1: Hacker inputs SQL code into a text field and submits the form. This is text above Browser 2
Step 2: PHP script puts the raw fields directly into the SQL query
Step 3: The resulting query is actually two queries
Step 4: All records in Users table are deleted when SQL code 2 is executed.
If SQL code 1 is executed then the User table is maintained but all the entries are removed.
Back