Long description
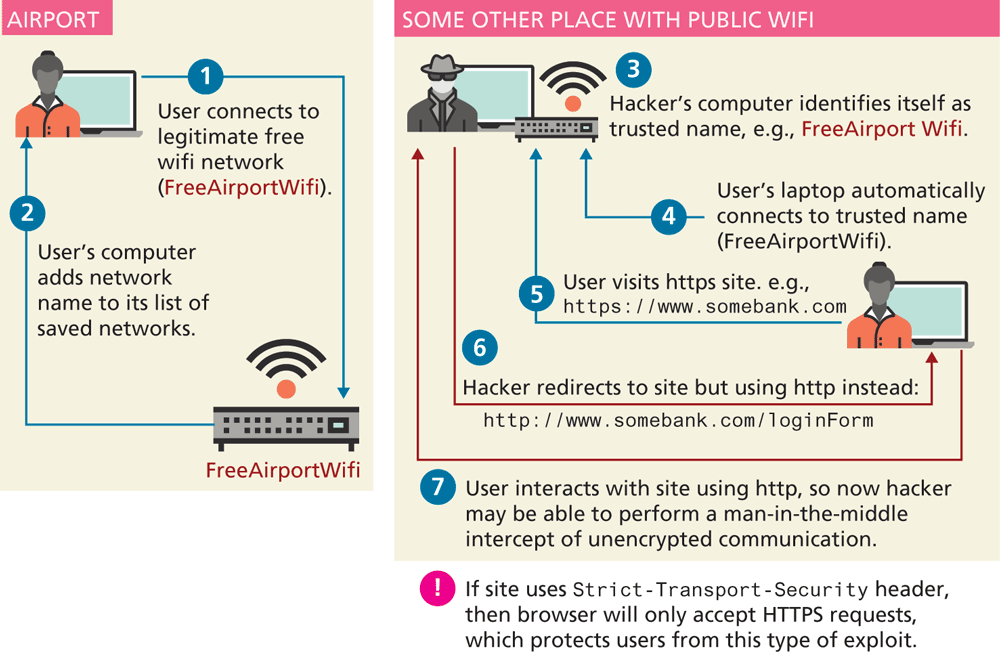
The first part of the image shows the Airport wifi management steps, and the second part shows the management steps in some other place with public wifi. An arrow from the user, labeled User connects to legitimate free wifi network, points to the Free airport wifi. An arrow from the free airport wifi points to the user. The second part shows the steps followed in some other place with public wifi. The hackers computer identifies itself as trusted name, e.g Free airport wifi. The arrows labeled the following points to the public wifi block:
Users laptop automatically connects to trusted name.
User visits h t t p s site dot e g h t t p s colon forward slash forward slash w w w dot somebank dot com.
Hacker redirects to site but using h t t p instead: h t t p colon forward slash forward slash dot somebank dot com forward slash login form. The user interacts with suite but using h t t p, so now hacker may be able to perform a man in the middle intercept of unencrypted communication.
Back