Long description
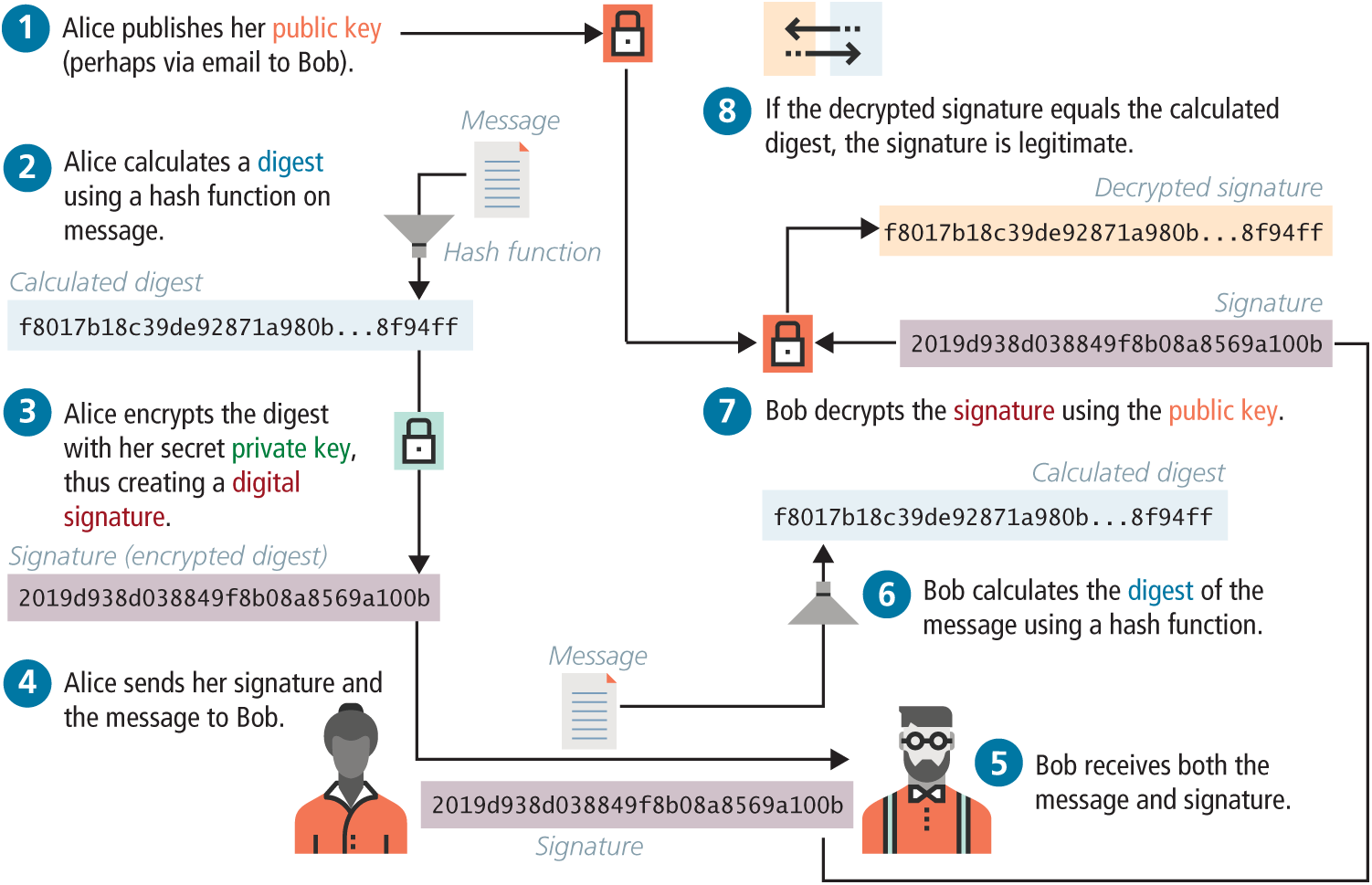
The Illustration of a digital signature and its validation shown in the image contains 7 steps:
Step 1: Alice calculates a hash of the message.
The outcome is the Calculated hash that reads as f 8 0 1 7 b 1 8 c 3 9 d e 9 2 8 7 1 a 9 8 0 b dot dot dot 8 f 9 4 f f
Step 2: Alice encrypts the hash with her private key thus creating a signature.
The outcome is the Signature that reads reads 2 0 1 9 d 9 3 8 d 0 3 8 8 4 9 f 8 6 0 8 a 8 5 6 9 a 1 0 0 b
Step 3: Alice sends the message and signature to Bob.
Step 4: Bob receives the message and signature.
Step 5: Bob calculates the hash of the message.
The outcome is the Calculated hash that reads as f 8 0 1 7 b 1 8 c 3 9 d e 9 2 8 7 1 a 9 8 0 b dot dot dot 8 f 9 4 f f
Step 6: Bob decrypts the signature using the public key.
The outcome is the Decrypted hash that reads f 8 0 1 7 b 1 8 c 3 9 d e 9 2 8 7 1 a 9 8 0 b dot dot dot 8 f 9 4 f f
Step 7: If the decrypted hash equals the calculated hash, the message is legitimate.
Back