Long description
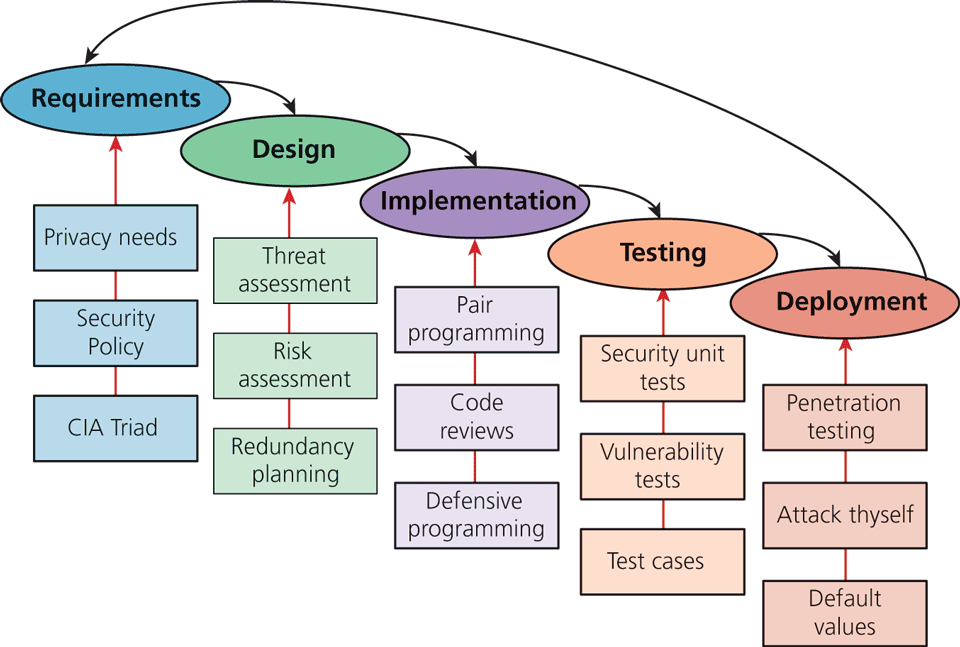
The figure shows a Software Development Life Cycle Model. The Requirement phase has C I “A” Triad, Security policy, and Privacy needs as security inputs. The Design phase has Redundancy planning, Risk assessment, and Threat assessment as security inputs. The Implementation phase has Defensive programming, Code reviews, and Pair programming as security inputs. The Testing phase has Test cases, Vulnerability tests, and Security unit tests as security inputs. The Deployment phase has, Default values, Attack thyself, and Penetration testing as security inputs. An arrow from each of the phases points to its next phase indicating the order of the process. An arrow from the Deployment phase points to the Requirement phase indicating the repetition of the S D L C cycle.
Back