Chapter 8. Catch Me If You Can
Blockchain and cryptocurrencies offer a lot of promise. However, the path to success is littered with ruts and pitfalls. Ever since it was first implemented, there have been various scandals, hacks, and thefts involving Bitcoin.
It’s important to know about and understand these events, because the past is capable of repeating itself if history is not used as a guide. Although the issues we describe in this chapter may seem severe, in the long run they will be seen as mere bumps in the road leading to a world of opportunity.
Probably the most famous nefarious example was Silk Road, an anonymous, illicit marketplace on the dark web that used Bitcoin as a payment mechanism. Users would log in to Silk Road using Tor, an anonymous virtual private networking (VPN) software. Tor uses a global network of computers to route internet traffic so it is almost impossible to trace. This allows users to remain anonymous by obscuring identifying information like IP addresses.
In October 2013, after a long investigation, the FBI arrested Ross Ulbricht for his role as the operator of Silk Road. They were able to catch Ulbricht by grabbing his encrypted laptop while it was open as he was working at a public library in San Francisco, California. The authorities were able to access everything on his computer, including incriminating information regarding the operations of the site. Ulbricht is now serving a double life sentence for operating what was at the time one of the largest marketplaces for illegal drugs, guns, and other contraband.
In the early days of Bitcoin, many users believed transactions on the blockchain would likewise be hard to track. However, over time a number of crypto-focused researchers and businesses discovered ways to link addresses to each other using metadata from exchanges, wallet providers, and other stakeholders in the ecosystem.
The Evolution of Crypto Laundering
Before 2014, when most people still thought bitcoin transactions were anonymous, many criminals assumed that moving dirty funds through crypto would keep their tracks hidden.
From 2011–2013, Silk Road was successfully using Bitcoin for payment. When funds were stolen from exchanges during this time, the common thinking was that there was no recourse. After the collapse of the Japanese exchange Mt. Gox in early 2014 (see “Mt. Gox”), followed by ultimately successful efforts by investigating authorities to trace the missing funds, many people began to realize that bitcoin transactions are not completely anonymous.
At that time, the only visibility people had into bitcoin transactions was using a blockchain explorer such as Blockchain.info (now Blockchain.com), as shown in Figure 8-1.

Figure 8-1. The first bitcoin transaction sent between two addresses, viewed in a public blockchain explorer
Many crypto exchanges did not perform KYC checks on customers, but authorities had yet not begun penalizing these exchanges for not doing so, making it easy for criminals to use them to convert funds from crypto to fiat.
Tip
KYC is a common term in regulation and compliance; it means Know Your Customer and refers to a process for verifying the identity of a user looking to open an account at a financial institution.
Around 2014, a few blockchain analytics companies began helping authorities follow the trail of funds relating to criminal investigations. People began to realize bitcoin was actually only pseudo-anonymous—an identity can be associated with a Bitcoin address. And since all bitcoin transactions are public, there is an entire transaction history, so it’s possible to determine relationships between different addresses.
There are many different ways to associate a Bitcoin address with an identity, including the following:
-
People may publicly identify themselves as the owner of a Bitcoin address. For example, some charities (and even WikiLeaks) post their crypto addresses for people to send donations to. Another example is Hal Finney, who posted on an online forum about how he had participated in the first bitcoin transaction, receiving 10 BTC from Satoshi Nakamoto. Studying this transaction reveals further information about Satoshi’s relationships, as shown in Figure 8-2.
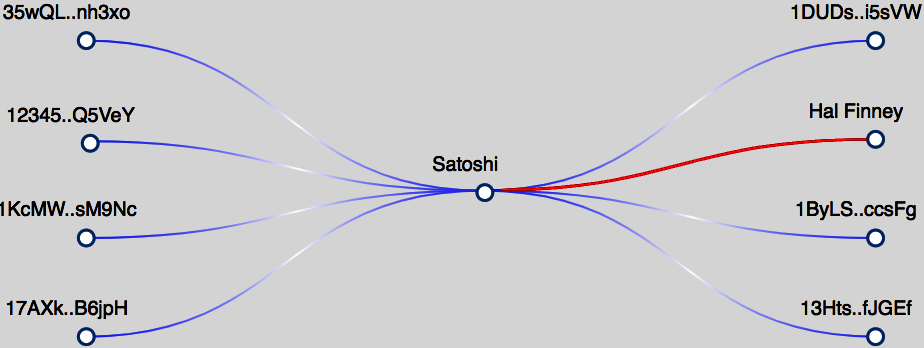
Figure 8-2. Screenshot from the blockchain analytics tool Breadcrumbs showing the other Bitcoin addresses Satoshi has a relationship with, including Hal Finney
-
Participants in a bitcoin transaction usually know the identity of the other party.
-
Many Bitcoin addresses are owned and managed by crypto-related businesses, including wallets and exchanges. Exchanges generate a unique Bitcoin address for each of their users and will usually have identity information for that user.
-
Evidence gathered from criminal investigations can sometimes connect a Bitcoin address to an identity. For example, after the authorities confiscated the Silk Road servers, they had all the bitcoin transaction information. They were able to trace the transactions to the Silk Road operator, but not necessarily all the participants.
Privacy advocates in the crypto community soon recognized that Bitcoin is not anonymous enough. This is why there are privacy-focused blockchains today that hide transaction details from the public. Monero is the most popular privacy blockchain.
From a criminal’s point of view, holding dirty funds is not ideal. Cleaning the funds and then spending them is the goal. There are three well-known stages of money laundering: placement, layering, and integration. Here, briefly, is how funds are laundered through cryptocurrency:
-
Placement: This stage is when the dirty funds are placed into a cryptocurrency. If the funds are in cash, the criminal must use some type of on/off-ramp to convert the cash into crypto. Many criminals can skip this step because the funds are already in crypto. For example, a merchant selling drugs on the dark web will receive payment in crypto.
-
Layering: This stage is when the funds are cleaned. In crypto, the most effective ways to do this are by moving the funds through either a tumbler/mixing service or a privacy blockchain like Monero.
-
Integration: This stage is when the funds are brought back into fiat and can be spent by the criminal. After cleaning the funds, the criminal must use an on/off-ramp to convert the funds back into fiat.
The layering stage can be done in a fully decentralized way, without depending on a central authority. However, the placement and integration stages require an on/off-ramp to convert funds between crypto and fiat. This is where the real battle in money laundering takes place.
There are many different types of crypto on/off-ramps, domiciled in many different jurisdictions, and they vary in how strict their KYC rules are.
Sophisticated money launderers will use fake or stolen KYC documents when signing up to a cryptocurrency exchange. Depending on how diligent an exchange’s compliance processes and employees are, some launderers succeed in misrepresenting their identity. Using false KYC documents protects the launderer from being identified in the event the exchange discovers that illicit funds are being laundered. However, the success of this approach depends on the processes the financial institution puts in place to prevent money laundering and terrorist financing. Many good operators will cross-reference document ID. Some will manually check the KYC docs, while others use tools like Acuant to check their validity.
FinCEN Guidance and the Beginning of Regulation
In terms of regulations and crime, 2013 was a pivotal year for blockchain networks. In addition to Silk Road being shut down, the Financial Crimes Enforcement Network (FinCEN), a US agency under the purview of the Treasury Department, issued its first convertible virtual currency (CVC) guidance. It states: “A user who obtains convertible virtual currency and uses it to purchase real or virtual goods or services is not an MSB (Money Services Business) under FinCEN’s regulations.”
However, it also states: “An administrator or exchanger that (1) accepts and transmits a convertible virtual currency or (2) buys or sells convertible virtual currency for any reason is a money transmitter under FinCEN’s regulations, unless a limitation to or exemption from the definition applies to the person.”
In other words, those who transmit money on behalf of others are required to obtain MSB licensing. FinCEN lists those types of businesses that are MSBs as follows:
-
Currency dealer or exchanger
-
Check casher
-
Issuer of traveler’s checks, money orders, or stored value
-
Seller or redeemer of traveler’s checks, money orders, or stored value
-
Money transmitter
-
US Postal Service
With the 2013 CVC guidance, this list also encompassed virtual currency operators, which may include exchanges, wallets, and other platforms that facilitate virtual currency transactions for users or customers.
When it comes to figuring out which bodies require compliance for what, the array of regulatory regimes can be confusing. A number of US agencies and regulatory bodies have laid claim on regulating cryptocurrencies. Here are the three major ones that have made clear some of the rules of the game:
- CFTC
- The Commodity Futures Trading Commission is in charge of regulating commodities, futures, and derivatives markets. The Commissioner of the CTFC has advocated a “do no harm” stance toward cryptocurrencies, noting the internet was able to flourish with a light regulatory touch. However, it is clear from CTFC statements that it will go after market manipulation and fraud. So far, the CFTC has claimed jurisdiction over Bitcoin and Ethereum and subsequent derivative instruments. The CFTC has an innovation unit to look at new technologies and meet with entrepreneurs, called CFTCLab.
- SEC
- The Securities and Exchange Commission has regulatory authority over securities. A security is defined as an investment contract, and a number of blockchain-based tokens that have been used to raise money may fall under that definition. In fact, the SEC has issued guidance on investment contracts for digital assets. It also has been open to providing no action letters for projects it deems suitable for avoiding the Howey test, a measure of whether an asset is a security or not. This is a process whereby a project or company will reach out to legislators to obtain a letter promising not to enforce rules retroactively. The SEC also has an innovation unit called FinHub to review blockchain and other financial technologies.
- NYDFS
- The New York Department of Financial Services regulates financial activities in the state. New York is the financial capital of the US, and the NYDFS is responsible for financial services and products there. In 2015, the NYDFS started requiring virtual currency operators to obtain a “BitLicense” to do business in the state. This includes exchanges, wallets, and other products/services that incorporate cryptocurrencies. Obtaining the license involves a 30-page application and a $5,000 fee, and putting together all the necessary information can cost upward of $100,000. Only about 25 companies operating in New York have a BitLicense.
The FATF and the Travel Rule
A new stipulation brought by the Financial Action Task Force (FATF), the Travel Rule requires more data sharing between cryptocurrency operators. The FATF is a Group of Seven (G7) intergovernmental group that includes the US, Canada, France, Germany, the UK, Italy, and Japan.
The standards require virtual asset service providers (VASPs) to provide user data when transactions occur, including moving funds from service providers such as exchanges. This data can include the following:
-
The sending customer’s name
-
The sender’s cryptocurrency address used to process a transaction
-
The sender’s physical identity number as a unique identifier
-
The receiving customer’s name
-
The receiver’s cryptocurrency address used to process a transaction
These rules may be new for cryptocurrency and blockchain companies, but they are not new for banking. They have been in place for banks to combat money laundering, terrorist financing, and other financial crimes for many years.
Any service provider in the cryptocurrency world that already has to submit to Money Services Business (MSB) standards is likely to have to do the same for the Travel Rule. A review of these standards is expected in 2020.
Skirting the Laws
Cryptocurrency and blockchain technology are interesting in that they intertwine with money, and this intertwining has caused a number of early adopters to have run-ins with regulators and law enforcement. It has definitely been shown that just because blockchain is a new paradigm doesn’t mean it is above the law. This section lists a few examples of people or groups that have been penalized by US enforcement agencies:
- Trendon Shavers
- Created Bitcoin Savings & Trust, a scheme that took in over 764,000 BTC by promising investors a 7% return per week via arbitrage trading. Shavers was sentenced to one and a half years in prison and ordered to pay $1.23 million in restitution in 2015. This is widely known as the first Ponzi scheme conviction and first US criminal securities fraud case in cryptocurrency.
- Charlie Shrem
- Facilitated bitcoin transactions as an unlicensed money transmitting business. Using his company BitInstant, Shrem helped a broker provide bitcoin without KYC/AML to users of Silk Road. Over $1 million in bitcoin transactions were conducted. In 2014, Shrem was sentenced to two years in federal prison and ordered to forfeit $950,000.
- Erik Voorhees
- Sold unregistered securities in two companies, FeedZeBirds and SatoshiDICE, in exchange for bitcoin. In 2014, the SEC settled with Voorhees for full disgorgement of the $15,843.98 raised (i.e., returning the funds to the harmed parties), and a $35,000 fine. Voorhees also agreed not to participate in any more unregistered securities sales using bitcoin or any other virtual currency.
- Carl Force
- Former Drug Enforcement Agency (DEA) agent; seized bitcoin under misrepresented DEA authority during the Silk Road investigation. Force also attempted to launder funds via Bitstamp and Venmo. Payment services froze his accounts, which he then attempted to get released using his DEA stature. He was sentenced to six and a half years in prison for money laundering, obstruction of justice, and extortion in 2015.
- Zachary Coburn
- Operated EtherDelta, an unregistered national securities exchange. EtherDelta was a smart contract–based platform that allowed users to trade Ethereum ERC-20 tokens. It was labeled a decentralized exchange, where no KYC/AML was required. Coburn paid $300,000 disgorgement, $13,000 in interest, and a $75,000 penalty to the SEC in 2018.
- Reggie Middleton
- Led Veritaseum’s ICO, which was investigated by the SEC as being an unregistered securities offering. Veritaseum raised $14.8 million from investors, purporting to offer a markets platform that didn’t require intermediaries. Middleton’s assets were seized during the investigation. His 2019 settlement included disgorgement plus interest of $8.47 million and a civil penalty of $1 million.
- Homero Joshua Garza
- Operated GAW Miners, a cryptocurrency mining firm that sold more units than it possessed in inventory. In this way, the operation acted like a Ponzi scheme. GAW Miners also sold customers “virtual miners,” or “Hashlets,” for future mining profits, which to the SEC appeared like securities. In 2018, Garza was sentenced to 21 months in prison for wire fraud.
- Mark Scott
- Acted as an attorney for OneCoin, a Ponzi scheme that generated billions in revenue. Scott was responsible for laundering $400 million of revenue through tax havens. OneCoin was a multilevel marketing operation that has seen prosecutions globally over false claims of its private blockchain-based cryptocurrency. Sentencing is still ongoing.
- Block.One
- Operated an unregistered securities offering via an ICO from June 2017 to June 2018. During that time the SEC released its DAO report, which covered a previous unregistered security offering in the cryptocurrency space as guidance for operators. The company was required to pay a $24 million settlement to the SEC.
- Enigma
- Operated an unregistered securities offering via an ICO in the summer and fall of 2017. Initially an MIT project that launched in 2015, Enigma raised $45 million selling ENG tokens. Enigma’s settlement with the SEC involved a fine of $500,000, registration of its token as a security, and the establishment of a claims process for harmed investors.
Avoiding Scrutiny: Regulatory Arbitrage
Regulatory arbitrage is a term for measures taken to avoid compliance scrutiny in heavily regulated jurisdictions like the US. This can be done in a number of ways, such as by falsifying the nature of transactions or switching geographical areas. It has long been a common practice in finance, and the blockchain industry has followed this trend by moving to various jurisdictions, including the ones discussed here.
Malta
In 2018, Malta enacted several laws aimed at fostering digital currency regulation. These include the Malta Digital Innovation Authority Act (MDIA), the Innovative Technology Arrangements and Services Act (ITAS), and the Virtual Financial Assets Act (VFAA). These rules put in place specific operating procedures for cryptocurrency businesses. As a result, a number of cryptocurrency and blockchain companies have incorporated in Malta.
An archipelago in the central Mediterranean Sea, Malta is not without controversy. Although it is a member of the EU, a number of scandals have engulfed the island state. Corruption, tax evasion, and fraud are common problems. The new regime installed in 2020 as a result of previous government misconduct may help to stem some of these systemic problems and foster cryptocurrency innovation in the country.
Singapore
Cryptocurrencies are treated as goods in Singapore, whether used for the purposes of trading, ICOs, or general sales. This is beneficial from a tax perspective, as Singapore’s Goods and Services tax is similar to the Value Added Tax (VAT) many other countries apply to saleable items.
Singapore has been forward-thinking and clear on its laws around cryptocurrency and blockchain. In 2020, the Monetary Authority of Singapore issued rules requiring AML and KYC laws be put in place for cryptocurrency companies. Concerns around money laundering, terrorist financing, and other criminal activity seem to have precipitated this, with the growth of ICOs as a financing method serving as a possible trigger point.
Hong Kong
Like Singapore, Hong Kong is a financial hub in Asia. One of the attractions of Hong Kong is the region’s tax policy. There are no capital gains taxes in Hong Kong, only a standard income tax rate. Cryptocurrencies are labeled “virtual commodities.” The leading financial regulator, the Securities & Futures Commission (SFC), has taken a hands-off approach to regulation, inviting some cryptocurrency companies to a “sandbox” program as a test.
The SFC has issued regulations for cryptocurrency exchanges that require a license. However, these requirements are for securities and other advanced products such as futures and derivatives. Regular cryptocurrency exchanges that trade assets like bitcoin are not expected to apply for such a license. This is because the registration is for professional investor exchanges, not retail. However, Hong Kong’s status as a separately governed entity from China may be in doubt, so this could change in the future.
Bahamas
Long known as a jurisdiction open to financial companies, the Bahamas is working to enact rules to enable cryptocurrency projects to domicile there. This includes the Digital Assets and Registered Exchanges (DARE) bill, introduced in early 2019. The bill is being constructed with feedback from cryptocurrency and blockchain companies prior to being passed into law.
In addition, the Bahamas has given out no action letters to various cryptocurrency projects. Although manipulation, tax evasion, and money laundering are still prohibited, the Bahamas is taking a forward-looking approach to cryptocurrency in order to foster innovation.
Crypto-Based Stablecoins
In the previous chapter, we discussed a few examples of stablecoins, which use blockchain technology to peg a cryptocurrency to another, more stable asset. For the most part, stablecoins are pegged to the US dollar, since it is known as a global reserve currency, but other assets have been used too, including gold, agricultural commodities, and the euro.
Many stablecoins are unregulated in the cryptocurrency world, although there are several stablecoin projects that are working with regulators and banks to foster a future where stablecoin assets are a large part of the ecosystem. While stablecoins attempt to stay pegged to their linked real-world assets, it is questionable whether they all have the requisite backing or liquidity to remain stable long-term. This has led to some of them running into difficulties in the past, and others becoming mired in legal problems. This section discusses a few examples.
NuBits
Introduced in 2014, NuBits was a stablecoin pegged to the US dollar. It used fractional bitcoin reserves, similar to how a bank keeps only a percentage of account balances, to “back” the stability of its token. Those reserves theoretically would allow it to absorb changes in the value of bitcoin. From 2014 to mid-2016, the price of bitcoin remained relatively stable. However, in 2016, as the price of bitcoin rose, NuBits lost its dollar-based peg for over three months.
At the end of 2017, NuBits then rose to a value higher than the dollar. This happened during a bull cycle in cryptocurrency, as enthusiasts were trading out of bitcoin, the project’s reserve, and into other assets, creating volatility. The lack of stability essentially caused many to jump ship, and its value has not recovered.
Digix
Known as a “gold token,” Digix was launched in 2014 to peg gold to a unit of cryptocurrency. The concept was to allow investors to own fractional or small amounts of gold, derived from London Bullion Market Association refiners, with one Digix token (DGX) worth one gram of gold. Digix is registered in Singapore and has been able to maintain a relatively stable peg to one gram of gold, although it doesn’t have a lot of liquidity, signaling a lack of demand. The Digix token is not listed on regulated cryptocurrency exchanges.
Digix was one of the first projects to launch on Ethereum, using a DAO smart contract structure with a token called DigixDAO (DGD) to raise funds, mostly in ether, for the project. In 2020, the DAO was shut down after a community vote, returning DGD to investors for ether. One of the problems with Digix is that the price of gold fluctuates in dollar value, a peg cryptocurrency traders prefer. However, it is an interesting example of tying a cryptocurrency to a real-world asset.
Basis
An ambitious project that sparked fervent interest within Silicon Valley, Basis raised $133 million in 2018 from prominent venture capitalists. Its aim was to create a decentralized token by creating incentives for traders to buy and sell what were referred to as bond and share tokens. This would then provide a stable asset for the market that could be utilized globally for a number of use cases, including applications in the developing world, crowdfunding, and exchange trading.
After the large fundraise, Basis started to confront the legal realities of being a US-based company launching a stablecoin. This included the bond and share tokens being recognized as securities by the SEC. In addition, KYC rules would have required Basis to keep a whitelist of users with authority to make transfers. After looking at several options, including centralizing the system, the project shut down and returned funding to its investors. It’s a common mentality in Silicon Valley that it’s better to ask for forgiveness than ask for permission, and Basis is an example of this.
Tether
Originally launched on the Omni protocol built on top of Bitcoin, discussed in Chapter 3, Tether (USDT) now reaches across several blockchains, including Ethereum, TRON, EOS, Liquid, and Algorand. Tether is nominally pegged to the US dollar and is by far the largest stablecoin in the cryptocurrency ecosystem, with over $15 billion in market capitalization in 2020. As a result of its prevalence across blockchains and exchanges, it is the most popular trading pair for moving into and out of more volatile cryptocurrencies (for example, ETH/USDT or BTC/USDT).
Tether is considered controversial, however. It is centrally controlled by Bitfinex, an offshore exchange. While supposedly backed by equivalent assets, there has never been a professional audit of its reserves. Tether has also been the subject of legal issues, including an investigation by the New York attorney general for the loss of an $850 million undocumented loan. Tether’s own attorney has also attested in court documents that one tether hasn’t always equaled one dollar of its own reserves, creating counterparty risk for those who trade USDT.
Initial Coin Offerings
As discussed in earlier chapters, ICOs are a way for founders to raise money for cryptocurrency projects. The process is fairly straightforward: an issuer looking to raise money for a blockchain-based project accepts one cryptocurrency, usually bitcoin or ether, and in exchange provides tokens representing a new cryptocurrency created as part of the project.
Note
ICO is a popular term for these projects, but other vocabulary is also used. Security token offering, token generation event, token offering, and token sale are other common names.
On July 25, 2017, the SEC released a report on the findings of its investigation into the ICO of The DAO, a project running on the Ethereum blockchain. As detailed in Chapter 4, The DAO was a smart contract–based decentralized autonomous organization created to raise money from cryptocurrency investors. A voting mechanism was put into place so that investors could then decide on various projects for The DAO to invest in, mostly revolving around blockchain or cryptocurrencies.
The DAO report concluded that this activity—the sale of tokens to investors—constituted the issuance of securities. It also indicated that US securities laws could apply to blockchains and cryptocurrencies in many instances. ICOs were an example of regulatory arbitrage in that ICO issuers were often ahead of the regulators. Despite this, as a result of The DAO investigation, out-of-court settlements in the ICO space have become common.
There have been thousands of ICOs launched since 2016, and they have significantly varied in quality. As Figure 8-3 illustrates, they range from well intentioned and viable to entirely fraudulent.
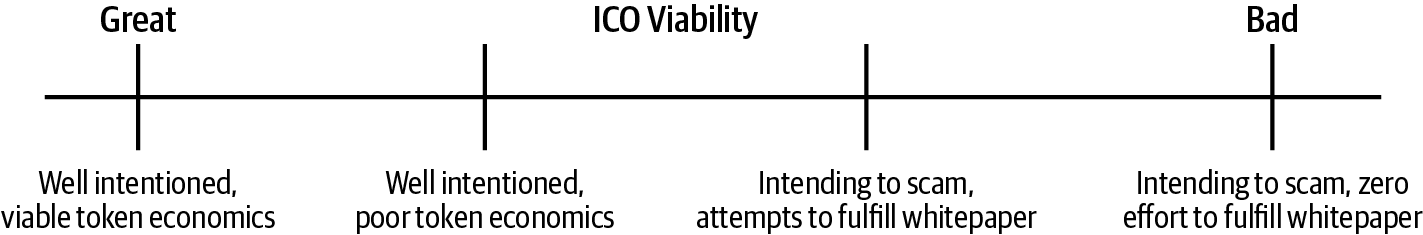
Figure 8-3. The spectrum of ICO viability
There are three main factors to consider regarding the long-term viability of an ICO: founder intentions, token economics, and the amount of effort put in to fulfill the promises made in its whitepaper.
Founder Intentions
The more passionate a project’s founder is about the problem a token is intended to solve, the greater the chances are that they will be very excited to spend the next 5 to 10 years solving it. Startups are tough. It takes a very high level of motivation and a talented team to get through the challenges involved. If the intention of the founder is to simply raise funds, then the project will focus on sales tactics. Usually once the sales goals have been met, time and resources will no longer be put into the token, leaving it to die.
Token Economics
Investors in a startup purchase equity in a business with the hope that the company’s value will increase and they can sell that equity later at a higher price. Generally, the value of a startup goes up over time if the business is able to grow. In an ICO, investors purchase a token with the hope that the token value will increase and they can sell that token later at a higher price; often it has nothing to do with business prospects.
Generally speaking, there are two types of tokens:
- Security tokens
- Similar to equity in a business, these tokens entitle the investor to part ownership in the business. Sales of security tokens fall under securities laws for the jurisdictions that both the buyer and seller are in, and have decreased in popularity as of 2020. Some of this has to do with the lack of security token exchanges and low liquidity on said exchanges.
- Utility tokens
- Utility tokens offer access to a product or service. When an investor purchases a utility token, it’s with the hope that demand for the product or service proposed by the project will increase significantly in the future. For example, if the project is an arcade, then the tokens might be the coins that game players need in order to play the arcade games. Investors will purchase these tokens in the hopes that demand for playing games at the arcade will increase and they will be able to sell the tokens later at a higher price.
Whitepaper
A whitepaper is a cryptocurrency project’s equivalent of a business plan. Some project founders will spend some investor funds to build a team and attempt to fulfill the promises made in the whitepaper. Projects with long-term viable token economies are usually able to articulately answer the following questions: Why does this product/service have to be on a blockchain? Why can’t you provide the same thing through a centralized database?
Most token projects cannot answer this question well and therefore have poor token economics. An example of a product/service that has to be on a blockchain is the Augur token (REP). Augur is a prediction market that requires regulatory scrutiny in many jurisdictions. If Augur were run on a centralized server, there would be increased capability to shut down the service by seizing the server.
Note
Motivations for those running an ICO are often not the same as for those running or investing in a venture capital–backed startup company. With a startup, the earlier an investor puts money into the company, the more equity they receive. Liquidating this equity is not possible until the company becomes so valuable that others want to purchase the equity, either through a merger, an acquisition, or a stock offering. This aligns the motivations of the founders (who have equity) and the investors who have purchased equity: to increase the value of the company. Token projects often receive millions of dollars of investment with minimal effort on the part of the founders, who also have the possibility of complete absolution from any liability. Because of this, with ICOs it can be extremely tempting for some founders to just take money for themselves and exit the company, either immediately or a little way down the road.
Exchange Hacks
As you know by now, “Not your keys, not your coins” is a popular saying in the cryptocurrency world. Centralized exchanges, which store private keys on users’ behalf, have often had troubles with security in the blockchain world. Exchanges offer a centralized attack vector that attracts thieves, and therefore exchanges are under constant assault. The story of Mt. Gox and what was discovered in the aftermath of its implosion is the best cautionary tale, but there have been a few other notable examples too. We’ll walk through a few of them here.
Mt. Gox
In early 2014, it was revealed that over 850,000 bitcoin had been stolen from Mt. Gox, a centralized exchange based in Tokyo. The theft was only discovered after it had been going on for several years, when the exchange was on the brink of collapse and was desperately trying to find investors for a bailout. Ultimately it did implode, although authorities in Japan have been able to organize a recovery effort to attempt to return funds to Mt. Gox users.
Launched in 2010, Mt. Gox was the first large cryptocurrency exchange. Over its lifetime it was victimized by multiple attacks, leading to thousands of people losing their funds. The following were the major incidents:
-
January 27, 2011: Hackers performed an XML injection that exploited a bug in the Mt. Gox payments platform. A now-defunct company called Liberty Reserve was facilitating customer withdrawals from Mt. Gox. When a customer requested a withdrawal on Mt. Gox’s website, the Mt. Gox servers made an API call to Liberty Reserve, and the bug was able to capture this information. A total of $50,000 was stolen through this exploit before the bug was fixed.
-
January 30, 2011: Shortly after the previous incident, a hacker tried performing a withdrawal of $2,147,483 through Liberty Reserve, and was accidentally credited $2,147,483 to their Mt. Gox account. The bug was fixed and the funds frozen before any funds were moved.
-
March 1, 2011: Just before ownership of Mt. Gox was transferred from founder Jed McCaleb to new owner Mark Karpelès, a hacker made a copy of the Mt. Gox hot wallet’s wallet.dat file and stole 80,000 BTC (wallet.dat files contain the private keys for a bitcoin wallet). As of 2020, the funds are still in the same Bitcoin address: 1FeexV6bAHb8ybZjqQMjJrcCrHGW9sb6uF.
-
May 22, 2011: Owner Mark Karpelès was in the process of figuring out where to securely store the Mt. Gox private keys, and his unsecured personal computer had temporary access to the files. Someone was able to access his computer, and stole 300,000 BTC. The thief gave back the stolen funds in exchange for keeping a 3,000 BTC fee.
-
June 19, 2011: A hacker gained access to an admin account for the exchange. They changed multiple account balances and crashed the market. During this time, they stole 2,000 BTC.
-
September 2011: A hacker gained read/write access to Mt. Gox’s database and proceeded to inflate their account balances, then withdraw funds. In total, they stole 77,500 BTC.
-
September 11, 2011: A hacker again managed to gain access to the Mt. Gox hot wallet’s wallet.dat file. This security breach went completely unnoticed, and from October 1, 2011 until mid-2013, the hacker continued to steal funds—a total of 630,000 BTC—from the exchange. Funds were occasionally credited to random Mt. Gox users, even though those users had never actually made a deposit. This led to the loss of an additional 30,000 BTC, as those users withdrew the funds.
-
October 28, 2011: Mark Karpelès had created new software to manage Mt. Gox wallets, but the code had bugs. When performing a withdrawal from the exchange, instead of putting the destination address bitcoin was supposed to be sent to, the new code would put a
NULLor0in the destination field. This led to a number of withdrawals from Mt. Gox going to addresses that no one had a private key to, meaning lost bitcoin. A total of 2,609 BTC was lost this way.
The biggest problem with these incidents was that they were mostly kept secret from the public, including customers and investors. At the time of its collapse, Mt. Gox was supposed to have generated 100,000 BTC of revenue and to have 950,000 bitcoin of customer funds in custody. But when the exchange shut down in February 2014, it only had 200,000 BTC in custody, and a total of 850,000 BTC—worth around $425 million at the time and much, much more today—was unaccounted for.
Efforts to track down the 630,000 BTC lost during incident 7 turned up the following:
-
The same addresses used to launder the stolen Mt. Gox funds were also used to launder funds from two other hacks targeting the exchanges Bitcoinica and Bitfloor (see Figure 8-4).
-
Most of the stolen funds were deposited into the now defunct exchange BTC-e, which was located in Russia.
-
The suspected operator of the BTC-e exchange was Alexander Vinnik. In July 2017, he was arrested in Greece over allegations that he had helped launder over $4 billion in funds through the BTC-e exchange. Court cases are still ongoing in 2020.
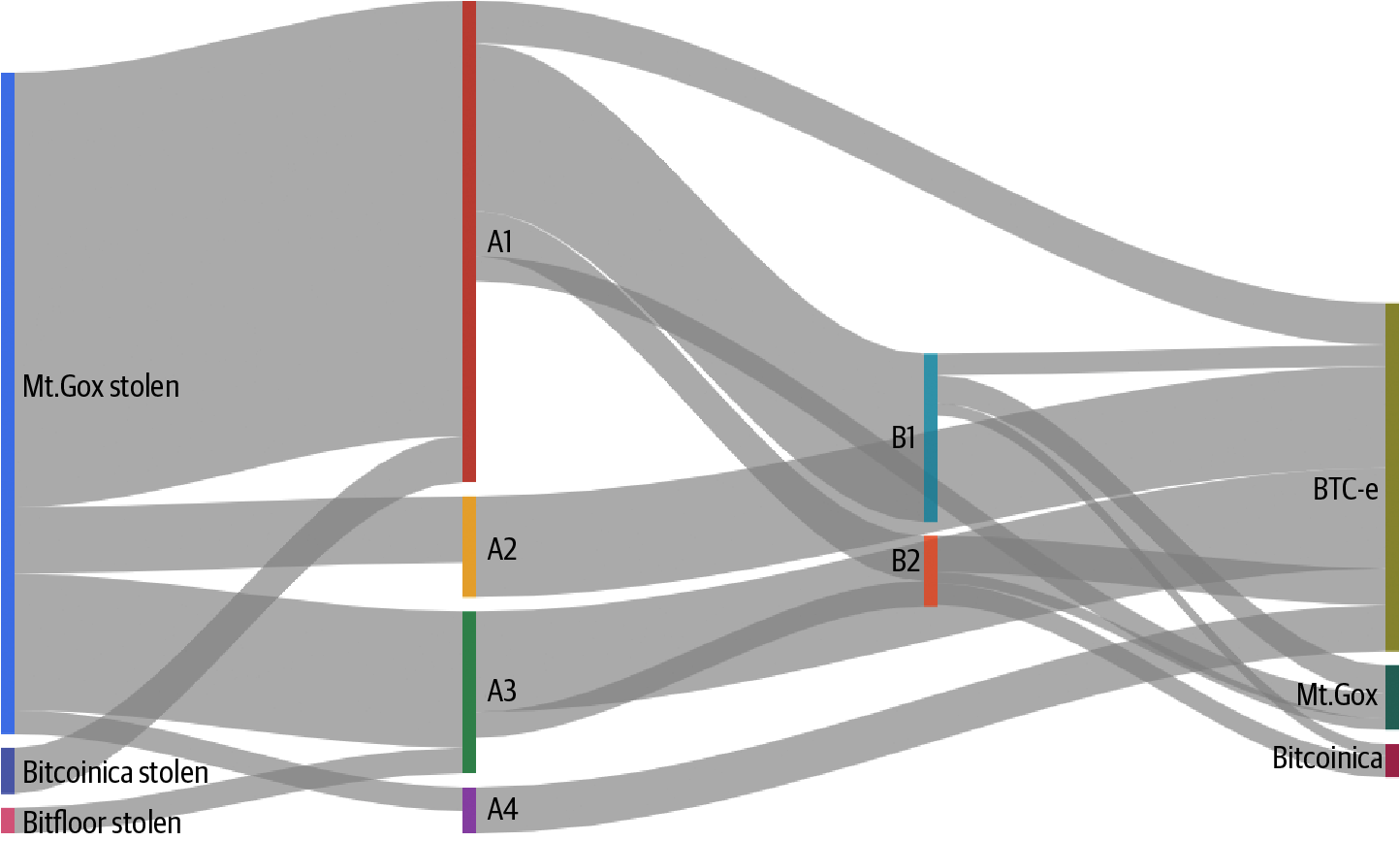
Figure 8-4. Flow of stolen funds through exchanges
Bitfinex
Nearly 120,000 BTC (worth about $72 million at the time) was stolen from Bitfinex, a centralized exchange based in Hong Kong, in 2016. Although Bitfinex used multisignature technology provided by the security company BitGo, the system was apparently compromised. In 2019, some of the funds from the hack began to move on the blockchain after remaining dormant for three years. The same year, two Israeli nationals were arrested for involvement in the hack and other schemes; they were accused of having stolen a total of $100 million worth of cryptocurrency.
Coincheck
In 2018, more than $500 million was stolen from this Japanese-based exchange, mostly in the NEM cryptocurrency. Coincheck did not utilize the basic security mechanisms that most exchanges used during this time, including keeping most customer funds in a cold wallet and implementing multisignature key technology. The exchange did take steps to label which tokens on the NEM blockchain were stolen to make it harder for the theft’s perpetrators to spend the funds.
NiceHash
A marketplace for miners to rent out hashing power, NiceHash was hacked in late 2017. Users started reporting that their cryptocurrency wallets were being emptied on the NiceHash website. A wallet address was identified as the location for the stolen funds, which totaled over 4,700 BTC (worth around $64 million), but they were not recovered. NiceHash resumed operations within weeks and promised to return the funds to customers via reimbursements on a monthly basis.
Other Hacks
Besides attacking exchanges, there have been a number of other creative ways cryptocurrencies have been parted from their owners. The following are some of the best-known. Hopefully these examples will help impart how important security is when owning crypto.
Bloomberg TV BTC Stolen
In 2013, Bloomberg TV reporter Matt Miller demonstrated some basics of bitcoin on-air. He gave other hosts $20 worth of bitcoin in paper wallets. One of the hosts, Adam Johnson, proceeded to open the paper wallet on live television, displaying its private key for about 10 seconds. A viewer named “milkywaymasta” was able to scan the private key’s QR code and stole the funds. As a lesson in key security, milkywaymasta promised to return the $20 if Johnson created a new wallet, since the old one could be “sweeped” because the private key had been shared publicly.
EtherDelta Redirection
In 2017, hackers were able to obtain personal information on the dark web about decentralized exchange EtherDelta’s operator, Zachary Coburn. The thieves were then able to set up call forwarding from Coburn’s cell phone, ensuring that all calls would be directed to a different number. After changing Coburn’s DNS settings and putting up a clone EtherDelta site, the hackers were able to steal at least $800,000 worth of cryptocurrency from one user.
CryptoLocker and Ransomware
CryptoLocker was an early and well-known variant of what is known as ransomware. Launched in 2013, this attack targeted Windows computers and spread via email attachments. It contained a Trojan virus that would lock up the user’s files using cryptography. In order to release the files, CryptoLocker demanded payment via vouchers or bitcoin. It infected over 250,000 computers and demanded an average payout of $300. Tracing Bitcoin addresses shows that CryptoLocker has been able to obtain millions from locked-out users. Ransomware has spread and proliferated since.
SIM Swapping
Michael Terpin operates a PR firm in the cryptocurrency industry. This made him a target of hackers, who took over $24 million in various cryptocurrencies in his possession. Nefarious actors were able to get Terpin’s wireless carrier to “swap SIMs,” transferring his phone number to a SIM card they controlled. The access they gained then allowed them to reset his exchange/wallet passwords. Terpin won a $75.8 million settlement in a civil judgment against 21-year-old Nicholas Truglia for the loss of funds.
Hackers often target well-known people in the blockchain industry with this hack because there is a high chance that those people hold a large amount of cryptocurrency. Most people who own cryptocurrency are not security experts and trust large companies to manage the deeply complex security steps required to protect their funds.
When a hacker targets someone to steal their crypto, they aim to break into their email. This is because an email account contains a significant amount of sensitive information and empowers the hacker to access many of the target’s internet accounts.
Here are the typical steps in a SIM swapping hack:
-
Find out the target’s phone number. It is common for people to include their phone numbers in an email signature or on a business card. Hackers may also be able to find a target’s phone number by purchasing it on the dark web if the individual’s personal information has already been compromised.
-
In the US, telecom carriers offer customers the ability to port their phone number to a different SIM card. This is extremely convenient when a telcom customer loses their phone, and wants to maintain the same phone number. Once a hacker knows the phone number of their target, they need to convince the telecom carrier to port over the target’s phone number. This can be done either through social engineering (by pretending to be the target requesting the phone port), by bribing a telecom employee, or through other creative methods.
After a SIM swap occurs, the hacker receives all of the target’s SMS messages. It’s very common for people to set their phone number as one of the recovery options for their Gmail account—it’s part of the sign-up process, as Figure 8-5 shows.
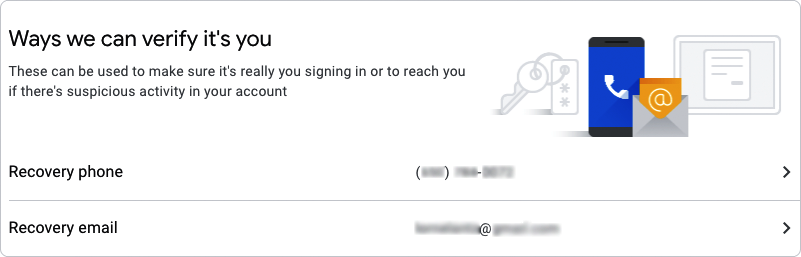
Figure 8-5. Gmail password recovery options include a phone number
Using SMS messages, a hacker can successfully complete the recovery process for an email account and gain access.
Once the hacker has control of a target’s email account, they can do all of the following:
-
Find out on which crypto exchanges the target has accounts, and reset the passwords. This is fairly simple with access to the email account. Many crypto exchanges send an SMS as the second-factor authentication (2FA), but the hacker has already compromised the user’s phone.
-
Access all documents in Google Drive. This might include private keys and sensitive business documents.
-
Access all photos in Google Photos. This might include QR codes of private keys, Google Authenticator keys, or even compromising photos that could be used for extortion.
-
Access the target’s passwords via chrome://settings/passwords, if the target is using Chrome’s built-in password manager.
-
Get the target’s entire contact list, which likely includes the phone numbers of many others in the blockchain industry.
As you can see, the list of damaging data a hacker gains access to is long. It may even include the target’s current location and schedule, via Google Calendar.
Armed with all this information, the hackers can break into crypto exchange accounts and withdraw all of the target’s crypto holdings. Since blockchain transactions are immutable, the target and the exchange have no ability to recover the stolen funds.
Consumer technology products constantly struggle to strike an ideal balance between convenience and strong security. Most of the vulnerabilities in SIM swapping are rooted in the fact that it requires users to put in effort to educate themselves about proper security practice. This includes, but is certainly not limited to, the following:
-
Using a PIN number for any account changes with a telecom carrier
-
Using a VoIP phone number like Google Voice for 2FA
-
Using Google Authenticator or a hardware device like a YubiKey for secondary 2FA
-
Using a secure password manager like 1 Password
Summary
The early days of cryptocurrency saw plenty of less-than-ideal activity occurring on blockchains. However, as regulators and law enforcement catch up with the technology, the promise of legitimate uses for blockchain has exploded. The next chapter takes a look at how businesses and other organizations are deploying blockchain applications to solve real-world problems—often with no cryptocurrency required.