Chapter 3. Forks and Altchains
Cryptocurrencies are still very much in a research and development stage, and developers have been trying for years to create another Bitcoin—a popular cryptocurrency network with a strong community behind it.
Whether because of scalability, functionality, or speculation, there have been a number of proposals for forking (more on this soon) the Bitcoin code into a new cryptocurrency with similar properties. Some of these ideas are quite novel, while others are simply a play to engineer value.
Bitcoin Improvement Proposals
Why not just change Bitcoin itself? It’s not that easy. There is a governance process that must be followed to update the Bitcoin protocol.
This is typical of software products: there is usually an internal process to identify continuous improvement opportunities. The process takes into account criteria such as who owns the product and who has a final say in its development, and determines when new features should be added.
Bitcoin Core is open source—the client software is open to everyone and is intended to be owned and managed by the Bitcoin community. Bitcoin Improvement Proposals (BIPs) are the community’s process to continuously manage and update the Bitcoin Core code. Instead of decisions being made by a designated committee or team, they are made by the entire community.
Anyone from the community who has an idea for improving Bitcoin can propose a new BIP. They must then champion the BIP to get consensus from the community that their proposal should be approved.
The life cycle of a BIP is as follows:
-
Someone from the community comes up with an improvement idea and proposes it to the BIP editors.
-
If the editors approve, they create a new BIP and put it into draft status.
-
If the miners signal support for a BIP, it moves into final status. It is the miners who need to be convinced to adopt a new BIP or not, because they are the ones who have to upgrade their software.
-
Once a BIP is in final status, the rest of the community must upgrade to the new software.
In order for a BIP to be accepted by the community, it must satisfy the following criteria:
-
It follows the correct format specified in the initial proposal outlining the process, BIP-0001.
-
It includes code that implements the change.
-
At least 95% of the past 2,016 blocks to be discovered were created by miners using the new BIP.
With that in mind, Bitcoin’s democratic process looks like this:
-
Anyone can propose a new bill.
-
The miners are voters, and the more hash power a miner has, the more votes they get.
-
The bill gets pushed into law if more than 95% of the hash power adopts the change.
Figure 3-1 sketches out the BIP process.
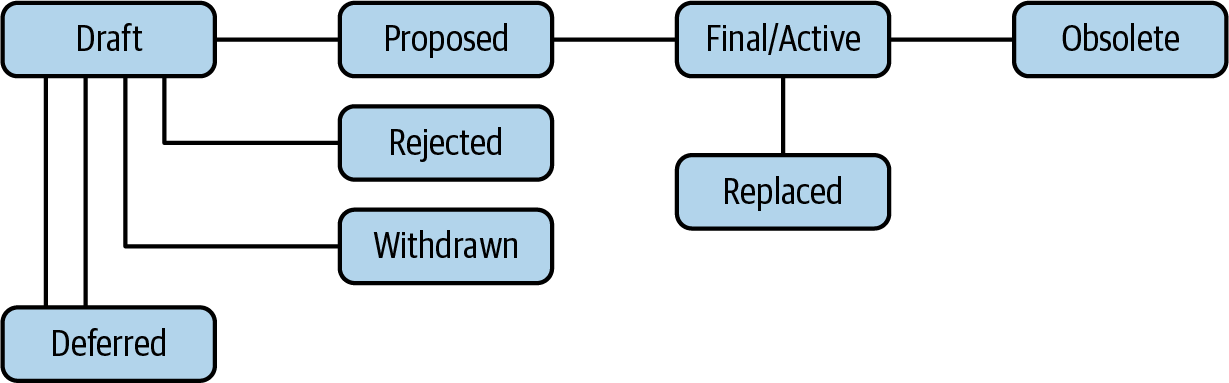
Figure 3-1. The Bitcoin Improvement Process
All BIPs are viewable on GitHub.
Understanding Forks
Once the Bitcoin community started to come together for the common good of the network, many programmers decided to software fork the technology, allowing them to create their own altcoins. Forking involves taking the Bitcoin Core software, changing some parameters, and launching it on mailing lists and message boards. The result is alternative coins, also known as altcoins. Some of these altcoins are so different from Bitcoin that it is better to refer to them as altchains.
Forking can actually mean a few different things in the cryptocurrency world. Here are some terms you may come across:
- Software fork
- This is a general term in technology systems and open source software. A software fork is when a developer takes a piece of open source software and changes some parameters to meet their needs. For example, the hundreds of different versions of the open source operating system Linux were created through software forks.
- Soft fork
- As it pertains to blockchain technology, a soft fork is an upgrade to mining software that makes a change to the network but does not require that all miners participate. This makes the upgrade compatible with older software, and is usually done to upgrade transaction functions.
- Hard fork
- As it pertains to blockchain technology, a hard fork is an upgrade to mining software that makes a change to the network that requires the participation of all miners. Hard forks typically implement key security or functionality changes, and the upgrades are incompatible with older software.
- Contentious hard fork
- In blockchain technology, a contentious hard fork is a backward-incompatible upgrade to mining software that makes a change to the network that is not accepted by all miners. Because some miners disagree with the fork and therefore don’t upgrade to the new software version incorporating the proposed changes, the blockchain effectively splits in two. All past records are the same on each branch, but beginning from the time of the contentious hard fork, the two chains have different transactions recorded on them and their software is incompatible.
Contentious hard forks can be problematic, so let’s dig into them a little more deeply.
Contentious Hard Forks
When a contentious hard fork occurs, the main blockchain of a cryptocurrency splits into two separate blockchains. This is what happened with Bitcoin Cash, a chain that diverged from Bitcoin in 2017, as illustrated in Figure 3-2.
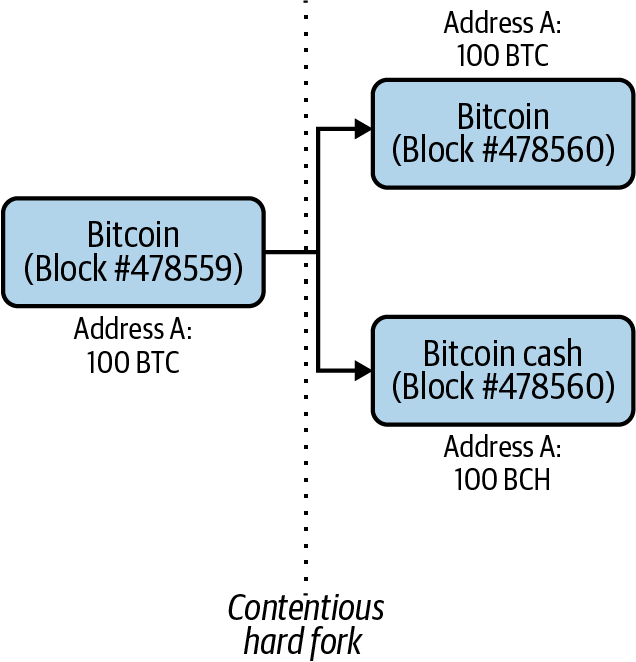
Figure 3-2. Blocks generated after the Bitcoin and Bitcoin Cash fork
Each blockchain inherits the history of the main blockchain before the fork. This includes every previous transaction, every address balance, every block hash, and so on. At the moment of the fork, the two blockchains have identical histories. After the fork, each blockchain creates its own new blocks and its own new record of transactions, and blocks can be mined by different miners.
In Figure 3-2, Address A has a balance of 100 BTC before the fork on the main Bitcoin blockchain. After the fork, two new chains split off of the main chain: Bitcoin (BTC) and Bitcoin Cash (BCH). Address A maintains a balance of 100 on both of the new blockchains, so it has 100 BTC on the Bitcoin blockchain (worth about $270,000 at the time of the fork) and 100 BCH on Bitcoin Cash (worth about $24,000). The previous Bitcoin chain (BTC) still exists as it did prior to the forking code being presented. Once the Bitcoin Cash nodes start accepting > 1 MB (megabyte) blocks, the Bitcoin Cash chain forks itself away from Bitcoin, creating the new chain.
Miners
Miners are the ones who contribute hash power to keep the network running. When a contentious hard fork occurs, the miners then decide which blockchain they want to support by either keeping the same software used by the preforked blockchain or changing to the software used by the forked blockchain. Figure 3-3 illustrates.
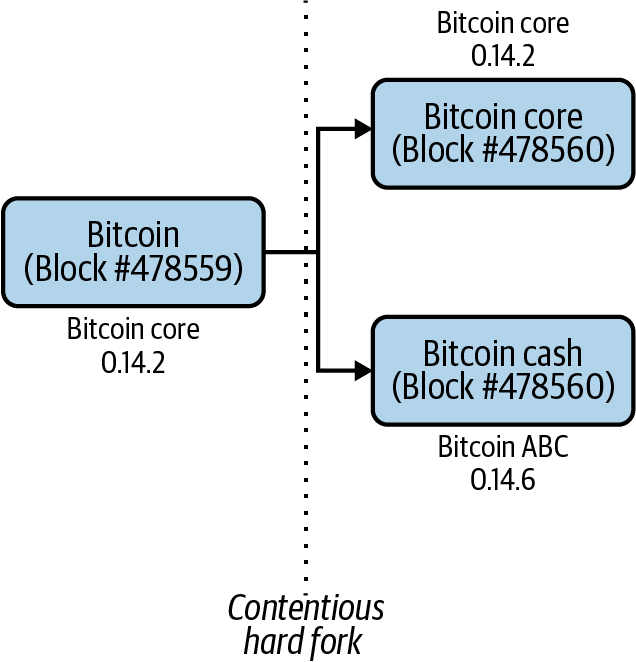
Figure 3-3. Bitcoin and Bitcoin Cash client versions after the fork
In the case of the Bitcoin Cash fork, the miners who wanted to support Bitcoin Cash changed their software to Bitcoin ABC v0.14.6 at block #478560, and began contributing their hash power to the new network. The miners who wanted to support Bitcoin continued using the same Bitcoin Core client, 0.14.2.
Note
Hash power is important to the survival of a proof-of-work–based blockchain. The more hash power is being contributed to a network by multiple parties, the more expensive it is for a single entity to take control of the network, and therefore the more decentralized the network is. And the more decentralized a blockchain network is, the more trust people have in it and in the security of that network. For example, say one blockchain has nine thousand nodes and another has just nine hundred nodes. The network with more nodes is more decentralized and will inspire greater trust.
So what happens then? When a contentious fork occurs, the community considers the blockchain with the highest hash rate after 2,016 blocks to be the “winning” blockchain, and the prize is that that blockchain gets to retain the prefork name. These names are extremely important because they are the names given to the blockchains on exchanges and have a big impact on the price of the cryptocurrency.
Today, Bitcoin has forked into three substantially different blockchains that the community continues to follow. They are Bitcoin, Bitcoin Cash, and Bitcoin SV (more on SV in a bit). As Figure 3-4 shows, Bitcoin’s hash rate is by far the highest.
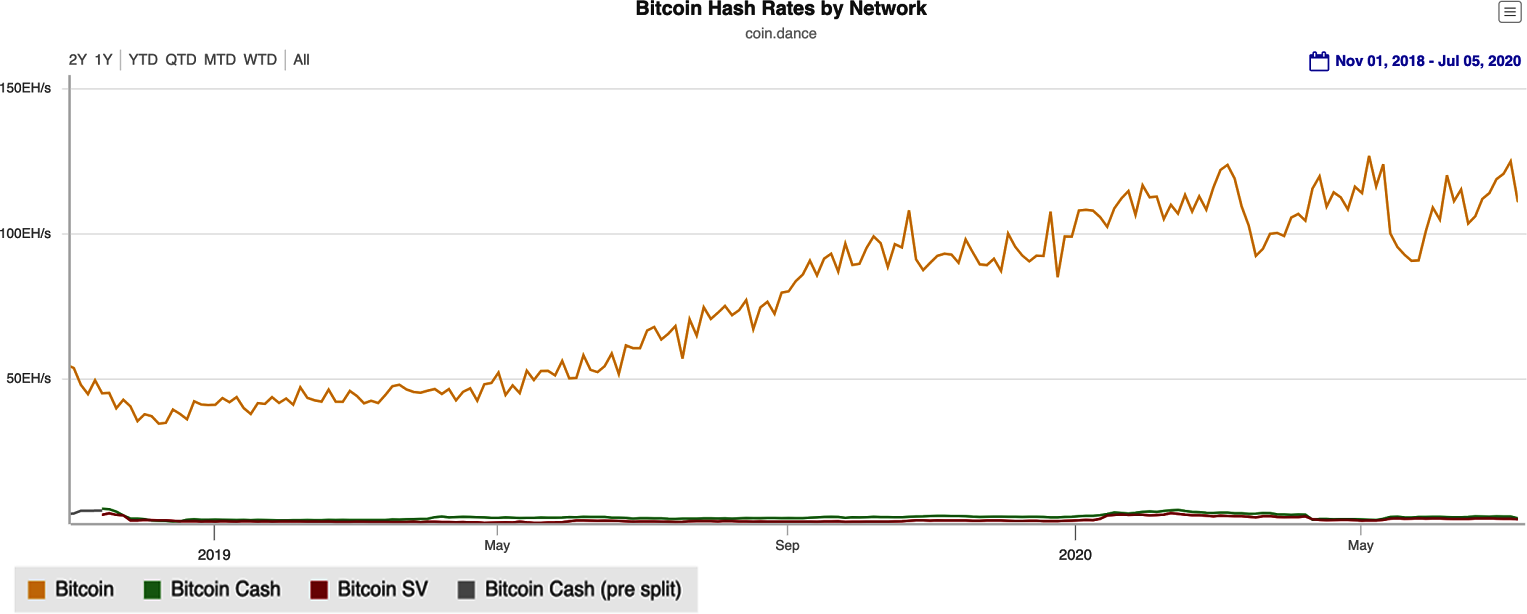
Figure 3-4. Hash rate of each network as of July 2020—Bitcoin’s hash rate is superior to its forks
Replay attacks
When a hard fork happens, both new blockchains become potentially vulnerable to what is called a replay attack. This occurs when an attacker takes data from a legitimate transaction on one blockchain and “replays” or mirrors that transaction on the second blockchain.
Two blockchains are vulnerable to replay attacks if they both have the exact same process for generating a transaction signature. Figure 3-5 shows what could happen if the Bitcoin and Bitcoin Cash blockchains were vulnerable to replay attacks.
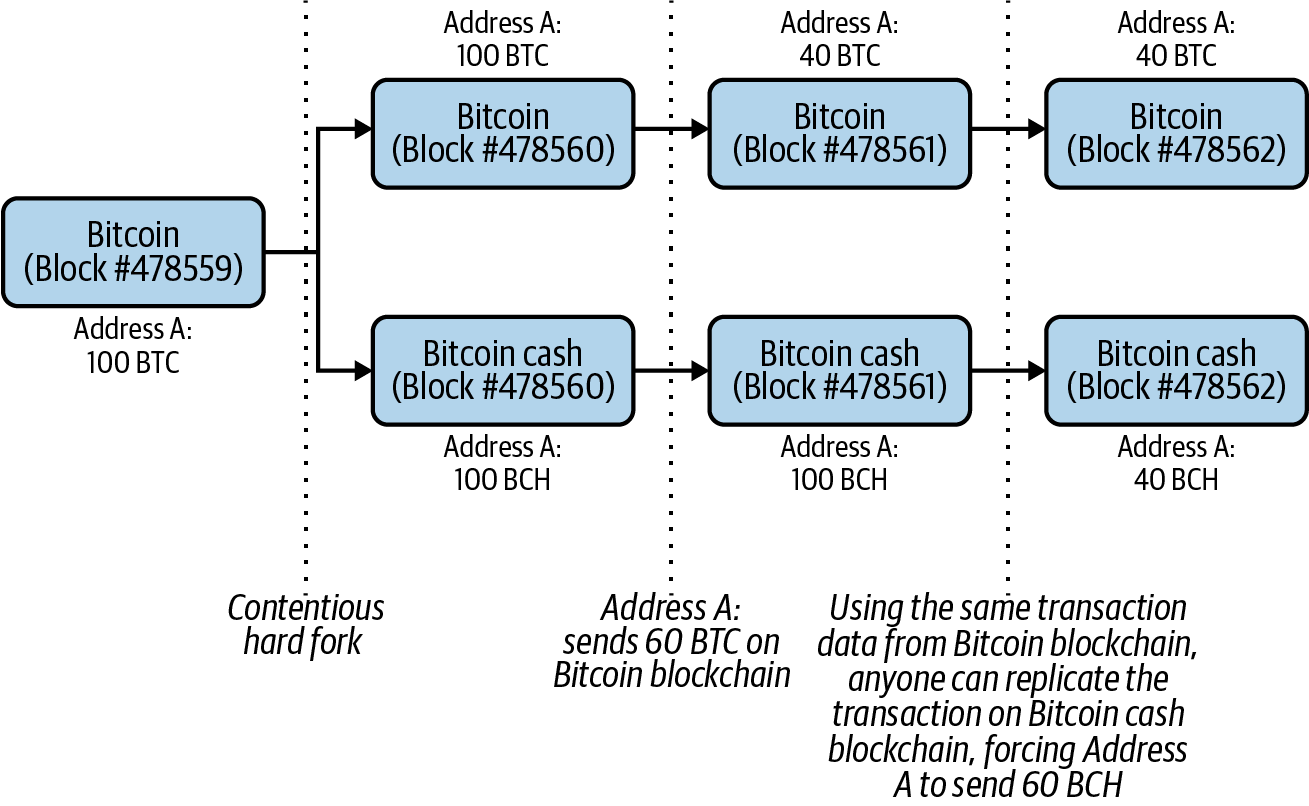
Figure 3-5. How a replay attack can happen after a fork
The sequence of events is as follows:
-
Address A broadcasts transaction instructions to the Bitcoin network that say to send 60 BTC to Address B.
-
The broadcast includes transaction data (that is, inputs and outputs) as well as a transaction signature. The transaction signature—a digital signature that ensures a transaction on the network is authentic—can only be generated by Address A using its private key and proves to the network that it has authorized the transaction on the Bitcoin network.
-
Since Address A has publicly broadcasted its transaction data and transaction signature, anyone can broadcast that same information out to the Bitcoin Cash network, and the network will process it because the two chains are similar.
Fortunately, when the Bitcoin Cash fork happened, the new software Bitcoin Cash miners were using included changes that prevented replay attacks from happening on either blockchain. Specifically, the Bitcoin Cash software added a new field called SIGHASH_FORKID to the structure of transaction data sent on its network. This field must be present in a Bitcoin Cash transaction in order for it to be valid. When the transaction signature is generated, one of the inputs to the encryption algorithm is the transaction data. Since the transaction data is structured differently on the two blockchains, signatures generated on the Bitcoin Core blockchain are different from those on the Bitcoin Cash blockchain and are not valid on the other chain.
Now that you’ve got a little background on forks, let’s look at the Bitcoin Cash fork in a bit more detail.
The Bitcoin Cash Fork
For a long time the cryptocurrency community considered the possibility of a split in the Bitcoin blockchain to be a bad thing, and there was uncertainty about whether the Bitcoin blockchain could survive with the community divided. But a debate over the future of Bitcoin and its ability to be used as money caused a rift between developers around 2015. One side wanted Bitcoin to be used as peer-to-peer electronic cash, as laid out in Satoshi Nakamoto’s original Bitcoin whitepaper. The other side wanted to limit the ability for there to be large volumes of transactions in Bitcoin’s blocks. This ultimately led to a split in the Bitcoin blockchain and the creation of the new Bitcoin Cash blockchain. And this is where the BIP came in.
Despite the implementation of solutions like SegWit and Lightning (discussed later in this chapter), there continued to be a group in the Bitcoin community that were unhappy with how the network was scaling, and particularly the issue of block sizes. Bitcoin’s block size was 1 MB, which limited the number of transactions in a block, and despite the proposed solutions, one group still maintained the easiest path forward was to increase the size of individual blocks. This group believed in Bitcoin’s original “peer-to-peer electronic cash” concept and wanted to see fast, cheap transactions, which larger blocks would facilitate. The other group, which had implemented SegWit and Lightning, believed that increasing the block size would make it too hard for individuals to run the Bitcoin Core software, as the overall blockchain would get too large and slow down the network. This disagreement threatened to stymie the decentralization of the network.
When the two sides failed to come to an agreement on scaling Bitcoin, ultimately a contentious hard fork was arranged. Mining hardware manufacturer Bitmain developed a plan for forking the community into two different blockchains. The mining pool ViaBTC coined the term Bitcoin Cash to reflect the idea that larger block sizes would make the new cryptocurrency more spendable, like cash, with lower fees and faster confirmation of transactions.
On August 1, 2017, the contentious hard fork occurred, creating Bitcoin Cash. The new blockchain featured 8 MB block sizes, giving each block roughly eight times the amount of transaction storage as Bitcoin offered. Most of the other features of the original Bitcoin chain remained, including the hard cap at 21 million units of cryptocurrency and the SHA-256 proof-of-work. In addition, anyone holding bitcoin at the time of the contentious hard fork received the same amount of Bitcoin Cash. Bitcoin Cash’s 8 MB block size, which was increased to 32 MB in May 2018, was designed to accommodate more transactions and features. While it has not garnered the traction many proponents expected, despite the controversy, Bitcoin Cash remains the most successful Bitcoin software fork.
Altcoins
The term altcoin is usually used to refer to forks of the Bitcoin Core software. The early altcoin frenzy began in 2011, after Bitcoin had gained some degree of traction, had gone through its vulnerability attack, and developers had begun to trust the technology. Here are some of the earlier altcoins:
- Ixcoin
- This fork was an early premined altcoin (see the next section for more on premining). After generating 580,000 coins ahead of time, the founder(s) launched Ixcoin on message boards and mailing lists with the idea that the original developer(s) would generate a lot of value for the existing premined coins. Suspicious of the premine, which enables some to enrich themselves before a blockchain goes live, the community forked Ixcoin into I0coin, which did not gain any traction even without premining.
- Solidcoin
- This fork sped up transaction confirmations with 3-minute block times, as opposed to Bitcoin’s roughly 10-minute confirmation time. With Solidcoin, fees were also constant, whereas Bitcoin’s are variable based on the sum of transaction fees in one block. However, fixed fees in Solidcoin created spam in the network, as attackers could simply attach fees to transactions and fill up blocks. The original developer decided they wanted more control, so they relaunched the project as Solidcoin v2 and required every other block to be mined by a centralized party. The project eventually lost traction.
- GeistGeld
- This fork drastically reduced the block time (the rate at which blocks are generated) to just 15 seconds. However, this became problematic as it was actually too fast for miners. It led to the creation of large numbers of orphan blocks that were not ultimately accepted into the chain, causing their transactions to be left behind, never to be confirmed. This made transactions difficult to complete on the network. The developers of GeistGeld also launched Tenebrix, the first cryptocurrency to use Scrypt mining. Scrypt is a more memory-intensive proof-of-work algorithm designed to deter the use of ASICs for mining.
- Namecoin
- Namecoin’s purpose was to act as a decentralized version of the Domain Name System (DNS), the system used to direct web traffic. When a user goes to google.com, for instance, DNS translates that address into a numerical location on the internet. The developers of Namecoin struggled to make the project both a cryptocurrency and a decentralized DNS, and it failed to gain traction. However, their idea of creating such a system and making the naming system more redundant raised the possibility of cryptocurrency being used for more than just transfer of value.
- Primecoin
- The proof-of-work for cryptocurrencies like Bitcoin typically involves solving random math problems, but Primecoin promoted the idea that finding prime numbers could prove to be useful. A prime number is a number that is only divisible by 1 and itself, and finding prime numbers becomes more difficult as numbers grow larger. Prime numbers are used in encryption systems, and as computers become faster at calculations, larger prime numbers need to be discovered. Primecoin became known as the first cryptocurrency to have a proof-of-work with a use beyond just confirming transactions, with the work focusing on searching for chains of prime numbers.
Litecoin
The best-known altcoin from the early era is Litecoin. In 2011, Charlie Lee, a developer at Google, began spending time playing around with the Bitcoin code. He had observed that other projects had launched with interesting ideas but had continually failed to succeed, for various reasons. One factor Lee identified was that the developers of early projects often remained anonymous, like Satoshi Nakamoto, but unlike Satoshi, they didn’t introduce groundbreaking new concepts; they only tweaked the Bitcoin code.
Another issue was premining, when a project mines or obtains cryptocurrency before its actual release as a public chain. If the developers of premined projects remained anonymous, it was hard to believe the projects would remain viable long-term because an anonymous founder who had premined could simply walk away at any time, taking their funds with them. Also, many of the early altcoins did not brand themselves well.
Lee thought deeply about creating something better. He thought of Bitcoin as a store of value similar to gold, and he wanted to create its silver complement. He also wanted to make his project “lite” so block times would be faster. Lee ultimately decided to give Litecoin four times the supply of coins of Bitcoin. In addition, the block time was set to be four times faster than Bitcoin’s.
Lee also decided to not premine, and to use the (in 2011) ASIC-resistant Scrypt algorithm to attract hobbyists. (ASICs are used in numerous technical applications—they use a specialized chip design to perform one task very well. Scrypt is another proof-of-work algorithm, similar to Bitcoin’s SHA-256 with some different properties.) With Litecoin using Scrypt, people could mine both bitcoin and litecoin at the same time on their computers. But eventually Scrypt would restrict bitcoin miners who wanted to use ASICs to profit from Litecoin because the algorithm was different. Developing Litecoin took Lee one week of planning and four hours of coding. It is still one of the top 10 cryptocurrencies by market capitalization.
More Altcoin Experiments
Lots more altcoins have been launched since the early era. A few interesting examples include:
- Dogecoin
-
Invented by programmer Billy Markus and marketer Jackson Palmer in 2013, Dogecoin is the realization of an internet meme crossed with cryptocurrency. Tweeting as a joke (Figure 3-6), Palmer suggested creating a cryptocurrency based on the internet meme of a Shiba Inu dog (doge). The idea gained traction, and an ecosystem formed around Dogecoin. Dogecoin is relatively inexpensive to acquire because there is no cap on the total number of coins, which keeps its price low.

Figure 3-6. Dogecoin started with a simple tweet
- Unobtainium
- Derived from an engineering term for an extremely rare element, Unobtainium was established in 2013. As its name suggests, the cryptocurrency has a very small number of coins in circulation—a cap of 250,000 units was set, to be mined over 30 years. Though an interesting experiment to try to create low inflation, Unobtanium experiences volatility like most other cryptocurrencies, and its daily trading volume is low (in the hundreds of dollars).
- Coinye
- Introduced in 2014, not long after Dogecoin, Coinye or Coinye West was the plan for a Scrypt-based cryptocurrency using rapper Kayne West as its meme/mascot. Almost immediately after the plans were announced, the developers received a trademark infringement notice from Kanye West. Although the team rushed to launch the coin, the legal pressure forced them to shut the project down.
- PotCoin
- Many banks still consider cannabis to be risky, so businesses with a license to sell pot often have to jump through many hoops. PotCoin, released in 2014, was the first attempt to create a cryptocurrency for the cannabis industry. Initially it was just a copy of Litecoin, but the project eventually moved to proof-of-stake velocity, which encourages staking, where a cryptocurrency holder profits from just holding it, and regular signing, which meant making transactions. Although PotCoin tried a number of marketing initiatives, market volatility and regulation made adoption difficult.
“2.0” Chains
In addition to forks from Bitcoin, there are also projects that have been built from the ground up. Indeed, many altchain ideas need to be built foundationally in order to accomplish the goals they intend to achieve. This section describes a few notable examples.
NXT
Launched in 2013, NXT was a very early “Bitcoin 2.0” or “blockchain 2.0” project. The idea was to create a more programmable, flexible blockchain. Instead of just having a cryptocurrency and a public ledger, NXT aimed to provide a platform for people to build applications on top of the system. It was one of the first to introduce the idea of a colored coin, which would tag or “color” a cryptocurrency to represent real-world assets such as property, stocks/bonds, or commodities. The NXT project was largely created and developed by an anonymous person or group. While it didn’t really take off, the concepts it introduced were important for other blockchains that came afterward.
Counterparty
Labeled as another of the first “Bitcoin 2.0” projects, Counterparty was launched in 2014. Like Mastercoin (discussed in Chapter 4), it was built on top of the Bitcoin blockchain but aimed to offer a lot more programming capabilities than its antecedent. Most notably, programmers were able to create their own crypto-based blockchain assets on the platform. It featured smart contracts, which contain code that provides a blockchain application with business logic, giving developers more control over when and under what conditions a block would be written to the blockchain (this concept is also explored more in the next chapter). Counterparty also has its own cryptocurrency, called XCP. Interestingly, to raise funds for the project, the developers took in around $1.6 million in bitcoin and “burned” it.
Privacy-Focused Cryptocurrencies
As we’ve mentioned, having a lot of data on a blockchain is not always ideal. After cryptocurrencies began to proliferate, many people grew concerned about how much financial data was being kept on the blockchain. Because of this, privacy-focused cryptocurrencies began to emerge. Two of the earliest projects in the privacy-focused area were Dash and Monero.
Dash
Launched in 2014, Dash is a software fork of Bitcoin. It went through less-than-reputable days when it was originally branded as a cryptocurrency called Darkcoin and was accepted as payment in online marketplaces where illicit goods were sold. The Dash protocol has an option for transactions called PrivateSend, which makes them untraceable by “mixing” them with the transactions of other users. In 2018, Dash implemented its own new type of ASIC-resistant proof-of-work, called X11.
Monero
Also launched in 2014, Monero uses something called the CryptoNote protocol for proof-of-work. CryptoNote uses a technology called ring signatures, a type of digital signature that can be used, for the purpose of hiding certain information, by a group of users owning keys. This system makes it impossible to tell whose key was used for signing, providing anonymity. Concepts like stealth addresses to hide destinations as well as ring confidential transactions to hide balances also lend to the privacy focus of Monero.
Zcash
Launched in 2016, Zcash is one of the most well-known privacy chains available today. Research has proven that in some instances, using hashes can compromise privacy in cryptographic systems. These systems could include blockchain-based cryptocurrencies, since they use hashes on a publicly viewable ledger. Zcash uses a technology called Zero-Knowledge Succinct Non-Interactive Arguments of Knowledge (zk-SNARKs) in order to enable privacy for its users.
zk-SNARKs allows users to transmit information between one another without having to share their actual data. Though that may sound confusing, there are instances where one party may not want to share private information with the other. For example, blockchain transactions allow both senders and receivers to easily see which exchanges, wallets, and other stakeholders the parties they’re transacting with use. zk-SNARKs prevents this.
Zcash has a fixed supply of 21 million units, just like Bitcoin. And like with Bitcoin, transactions can be transparent; users must implement a z-addr in order to “shield” a transaction. During Zcash’s launch, the price of one coin reached over $1,000 because of the hype surrounding the technology. However, most transactions on the Zcash network don’t use the privacy capability; research has shown only 3.5% of Zcash coins are held in shielded addresses.
We’ll talk a little more about these and other issues of privacy in Chapter 7.
Ripple and Stellar
There has been a good deal of criticism directed toward Bitcoin-based proof-of-work consensus, which has trickled into other cryptocurrencies due to software forks. One of the problems with the existing mechanisms is that there is an increasing degree of centralization happening in cryptocurrency networks such as Bitcoin. For example, over 65% of all Bitcoin mining is done in China, according to the Cambridge Centre for Alternative Finance. Ripple and Stellar, which share some founders and technical traits, are cryptocurrencies that don’t use proof-of-work mining and have had some success.
Note
As Bitcoin mining continues to require ever-larger amounts of computer processing power, the number of entities controlling that power dwindles, and a larger share of the mining is thus done by only a few entities.
Ripple
Initially released in 2012, Ripple is one of the earliest and longest-lasting alternatives to Bitcoin. Unlike a number of alternative cryptocurrencies from that time, the identities of Ripple’s founders are known: Jed McCaleb, who founded the Mt. Gox bitcoin exchange, is one, along with Arthur Britto and David Schwartz. There was even a company, Ripple Labs, formed to support the Ripple blockchain and its native currency, XRP. Ripple Labs is the largest contributor to the code for XRP and its blockchain, more commonly referred to as a ledger.
While early on Ripple was an open source competitor to Bitcoin, with third-party “gateways” that functioned as a method of anonymous exchange, in 2014 the company pivoted to supporting banks as a faster and cheaper settlement network with a cross-border focus. Instead of using traditional proof-of-work, Ripple introduced a new type of consensus known as the XRP Consensus Protocol. It uses Byzantine fault-tolerant agreement, which requires nodes to come to agreement on transactions.
Ripple has hundreds of partnerships with various companies in the banking and payments sectors. The best-known strategic partnership is with the money remittances company MoneyGram, in which Ripple has made a $50 million equity investment. MoneyGram uses Ripple’s On-Demand Liquidity product to facilitate cheaper and faster cross-border payments.
Stellar
Launched in 2014, Stellar was founded by Jed McCaleb and Joyce Kim, who had both previously worked at Ripple. The Stellar protocol is supported by the 501(c)(3) nonprofit Stellar Development Foundation, created with the aim of providing a low-cost payment network for underbanked or unbanked individuals across the world.
In the early days, Stellar used a similar consensus mechanism to Ripple’s. However, the Foundation changed the protocol in 2015, switching to SCP, a system devised by Stanford professor David Mazières. One of the reasons for switching from the Ripple-designed consensus mechanism was that the Stellar blockchain unexpectedly forked in 2014, creating two separate networks and causing problems with transactions.
After the departure of Joyce Kim, the Foundation began a long pivot, founding a company called Lightyear.io in 2017 (which became Interstellar in 2018 after acquiring the blockchain company Chain) to promote and encourage adoption of the protocol. Like Ripple, Stellar is focusing on cross-border payments, albeit with a more unbanked and underbanked bent, attempting to provide services to those who lack financial access.
Scaling Blockchains
In technology terms, scaling is the ability of a network to dynamically change resource allocation while improving or maintaining efficiency. Scaling has been a challenge as Bitcoin has grown: as more transactions end up on the blockchain, the network needs to continue providing a cheap and easy way to transact.
As configured today, Bitcoin’s blockchain can only handle three to seven transactions per second. Compare that to Visa’s payment network, which can complete 65,000 transactions per second. What’s more, when the Visa network needs to scale, its administrators can just adjust the allocation of resources. Visa owns the data and applications that run on its servers and controls access through central administrators.
But unlike Visa, which is centralized, Bitcoin is distributed. It runs across many computers and has no central point of control. In order for the Bitcoin network to grow, many industry stakeholders have argued that something needs to change—namely, the number of transactions that can go in each public printing of the ledger needs to be enlarged. Whether this can be done through larger blocks, less information in each block, or a larger number of blocks has long been debated.
Some stakeholders promote moving things off-chain, an option we’ll explore in Chapter 10. Despite this, there is still a great need for technical solutions for scaling blockchains. We’ll look at a few of the solutions that have been implemented here, and come back to this topic in the final chapter of the book.
SegWit
By 2015, a bottleneck in the Bitcoin infrastructure had become apparent—there were many more transactions waiting to be processed than could fit into each Bitcoin block. For example, 10 transactions might be requested per second, but no more than 7 of these could be processed. When there’s a bottleneck, 7 transactions get processed and the other 3 remain in the mempool, which contains pending transactions. This became problematic in that it slowed transaction times on the network. It also meant Bitcoin fees could become very expensive as users would have to compete to have their transactions recorded in a block, causing a “fee market.” One proposition to counter this problem was to implement a technology called Segregated Witness, or SegWit.
SegWit was originally proposed in 2015 by Bitcoin Core developers Eric Lombrozo, Johnson Lau, and Pieter Wuille. It moved some data, known as the witness portion, to a different part of each transaction. That data was then excluded from the block size calculations, effectively reducing the overall space needed for each transaction in a block (see Figure 3-7). This allowed more transactions to be stored in each block, effectively increasing the transaction throughput. It also solved the transaction malleability problem, an exploit that could allow an attacker to change the unique identifier of a bitcoin transaction before it is confirmed into a block. By July 2017, miners on the Bitcoin network had “locked in” an upgrade to the core software to implement SegWit. In August 2017 SegWit was activated, meaning it was put into use on the network.
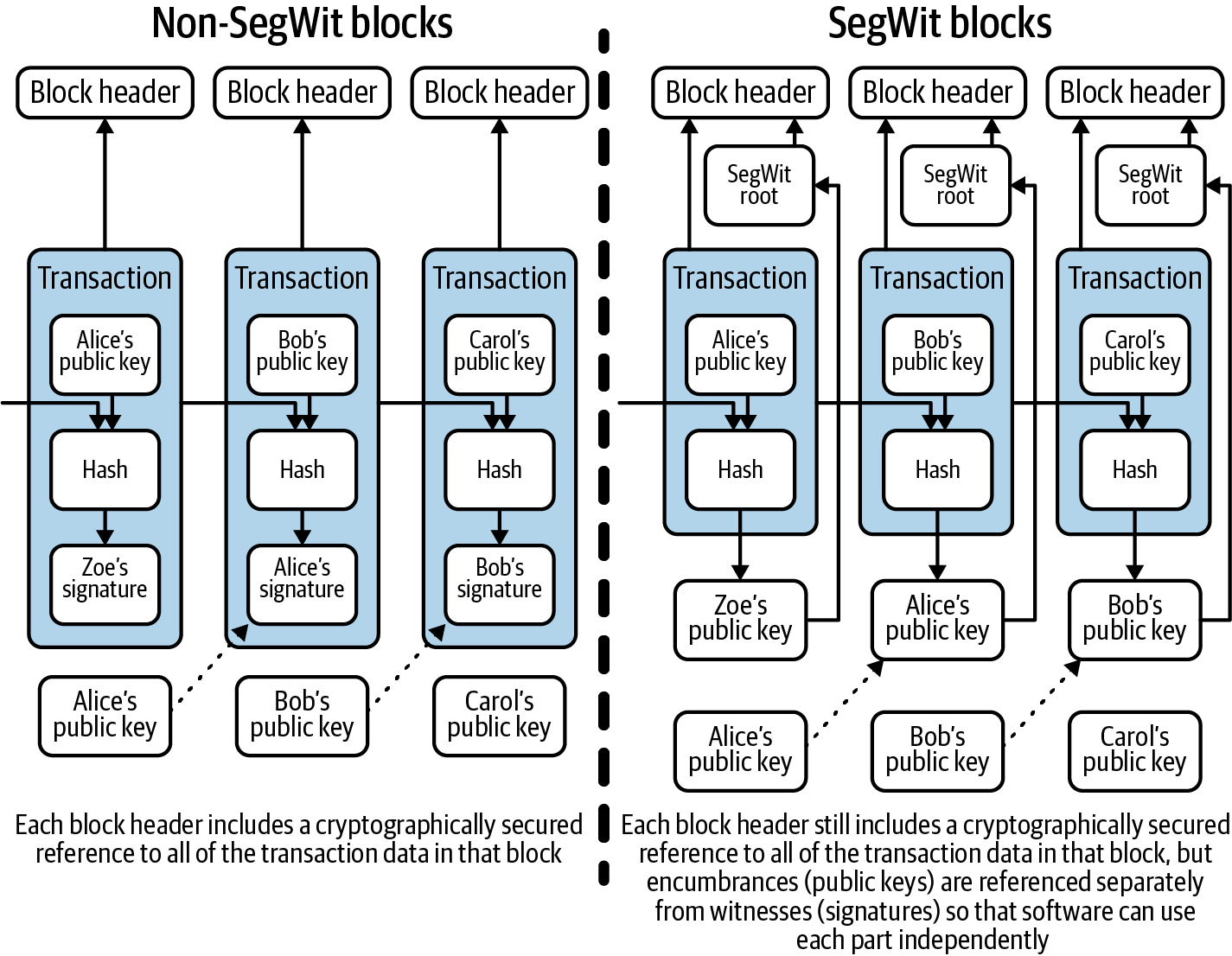
Figure 3-7. Technical comparison between SegWit and non-SegWit blocks
Lightning
The implementation of SegWit also created the technical preconditions for another scaling solution called the Lightning Network, proposed by Joseph Poon and Thaddeus Dryja in 2016. Lightning puts some bitcoin transactions on a separate “channel,” taking them trustlessly off the main Bitcoin blockchain. This allows Bitcoin to continue to grow without the need to fill up the blockchain with so many transactions. That means more uses for Bitcoin—such as consumer payments and microtransactions, which have become problematic as blocks become full and fees increase—might now be possible.
So how does it actually work? Instead of requiring miners and blocks to confirm transactions, the Lightning Network uses signatures between parties to digitally verify the sending and receiving of cryptocurrency (not just Bitcoin—Stellar has implemented a version of Lightning as well). This is done via the use of bidirectional payment channels. Users must create a channel on the network and post what is known as a funding amount, which does appear on the blockchain. The network uses a multisignature system called Hash Time Locked Contracts to enable multiple parties to transact with one another.
It is possible that the Lightning Network has some security risks. For example, Lightning experienced a distributed-denial-of-service (DDoS) attack in 2018, taking down 20% of the network. The exploit used as many nodes as possible in order to block connections from occurring. Another problem with Lightning is that nodes must stay open for transactions to happen between two parties. In addition, there are concerns about the prevalence of fraud on the network, which may necessitate the inclusion of “watchtower” nodes to monitor transactions for possible fraudulent activity.
Other Altchain Solutions
The most common solutions to increase the speed at which blockchain transactions can be processed are called state channels and sidechains. The Lightning Network is an example of the former in Bitcoin. An example of an implementation in Ethereum is a project called Raiden. State channels don’t use a separate blockchain, whereas sidechains do; an example is the Plasma implementation. Recently, there has also been a lot of talk about Rollups—specifically Zero Knowledge (ZK) Rollups, which present and publicly record validity without a verifier knowing the actual information for privacy purposes, and Optimistic Rollups, which use smart contracts to aggregate transactions off-chain and therefore store more information in each block.
Rollups is a scaling solution similar to Plasma, except Plasma has a data availability problem. With Rollups, thousands of transactions can be “rolled up” off-chain, which helps with scalability. It is estimated that the realistic throughput for Optimistic Rollups is around five hundred transactions per second (TPS, a metric used to define the speed of a blockchain), whereas ZK Rollups can manage around two thousand TPS. Of course, there is more to it than TPS, such as different security models and trusted setups, but discussing those is beyond the scope of this book.
Another scaling solution that Ethereum and other projects like Zilliqa and NEAR have been exploring for some time is sharding. This involves splitting the entire network into multiple network segments, termed shards. Each shard contains its own independent state, meaning a unique set of account balances and smart contracts.
Sharding allows the system to process many transactions in parallel, thus significantly increasing throughput. Although this helps with scaling, there are also some problems associated with it, such as the risk of a single-shard takeover attack, where attackers are able to take over a single shard due to the reduced hash power, and cross-shard communication complexity, where messages sent across shards may not be synchronized. When the network is sharded, essentially the security is also sharded, or reduced to individual parts. Ethereum intends to solve this via random sampling of validators on each shard.
The Ethereum Classic Fork
The Bitcoin Cash fork was planned, and the developers of the new blockchain had the foresight and time to implement replay protection into their software. The first Ethereum fork (more on Ethereum in the next chapter) that created Ethereum Classic was another contentious fork, yet the software updates did not include replay protection.
The Ethereum Classic fork happened in June 2016, in reaction to a $50 million hack that exploited critical vulnerabilities in the implementation of a smart contract called The DAO (the DAO hack is also discussed in Chapter 4).
The Ethereum community was divided into two groups:
-
One group wanted to update the Ethereum code to reverse the DAO hack.
-
One group wanted to keep the software as it was because reversing the transaction would mean that a single entity could control the network, which would diminish the value of the network being decentralized.
On Ethereum block #1,920,000, most Ethereum miners updated their software to the new code that reversed the hack, and that blockchain is still considered to be Ethereum in 2020. The Ethereum miners who continued using the same prefork software began mining the forked blockchain, called Ethereum Classic.
The updated software issued to Ethereum miners to reverse the hack was developed and published quickly and did not include replay protection. Both blockchains were vulnerable to replay attacks for five months. During this time it was up to wallet holders to implement a workaround to protect against replay attacks.
One way in which wallet holders protected themselves was to send the funds on each blockchain to different addresses that they controlled. As seen in Figure 3-8, if a user has 10 ETH in Address A, they will generate Address B on the new Ethereum blockchain, and generate Address C on the Ethereum Classic blockchain. On the Ethereum blockchain they will then move 10 ETH to Address B, and on the Ethereum Classic blockchain they’ll move the 10 ETH to Address C. After the funds are distributed to separate addresses, if someone attempts to do a replay attack on their funds, it won’t work because the balance of funds on each blockchain will be different.
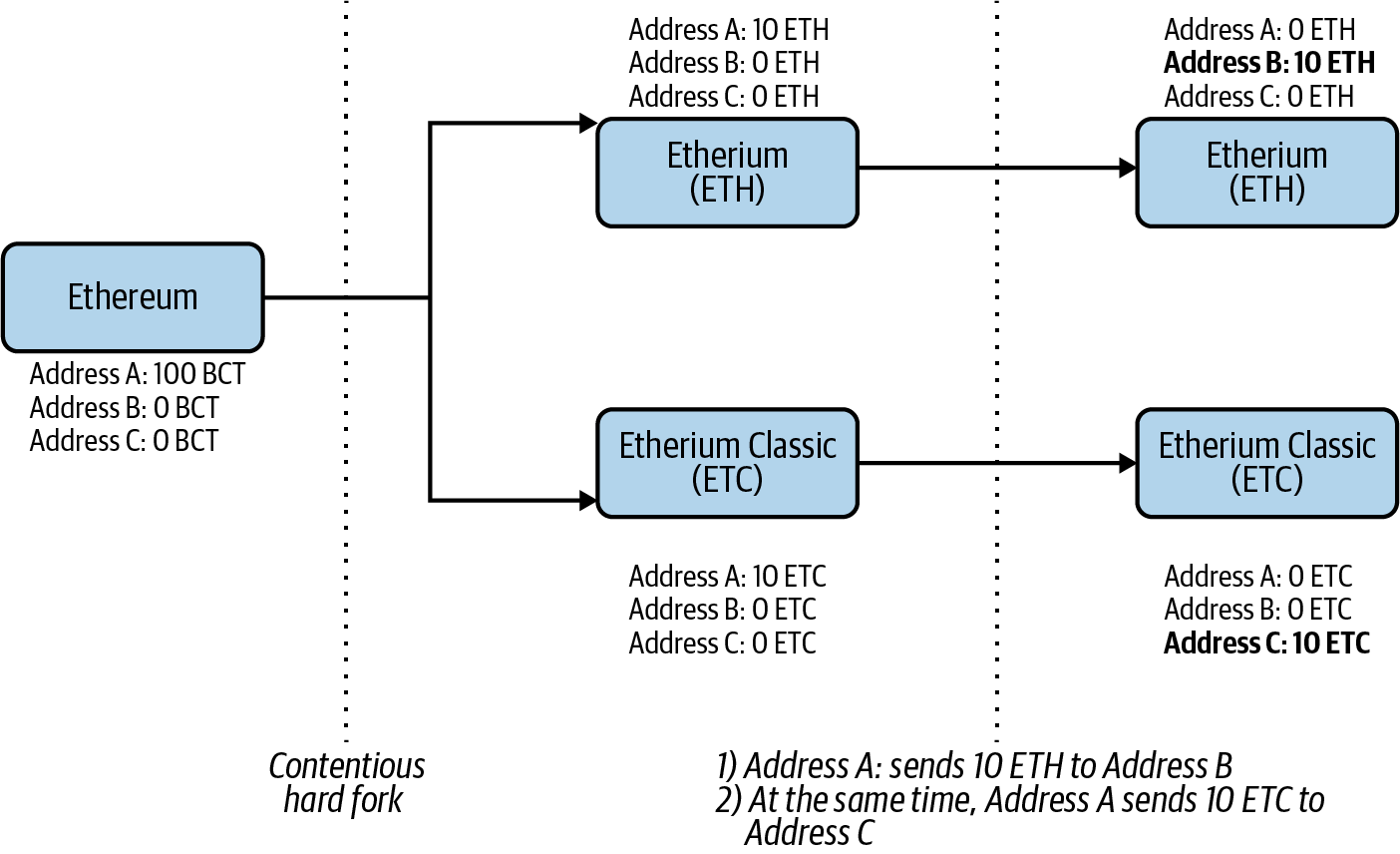
Figure 3-8. Protecting against replay attacks on Ethereum (ETH) and Ethereum Classic (ETC)
Exchanges that had the resources and expertise to protect against replay attacks were not affected. However, some individuals did lose funds due to the vulnerability. The Ethereum blockchain implemented replay protection in November 2016 through Ethereum Improvement Proposal 155 (EIP155), which was included in something called the Spurious Dragon hard fork.
Summary
Altcoins and altchains are fascinating explorations of what can be done with blockchains and cryptocurrencies. While numerous variations have been proposed, the majority of the projects described in this chapter build off the foundation of Bitcoin or Ethereum. Understanding what has already been tried is important. Many developers who come into the ecosystem may think a concept hasn’t been attempted before, but a little history lesson might tell them otherwise.