What Is Blockchain Technology?
You will see the phrase ‘blockchain technology,’ or commonly just ‘blockchain,’ in many different contexts, and it can be confusing because different people use the words to mean different things. Purists will have a different understanding of the word from generalists. Angela Walch, Research Fellow at University College London—Centre for Blockchain Technologies, provides some excellent commentary on the lexicon in her 2017 paper ‘The Path of the Blockchain Lexicon (and the Law)’.199 In general, technologists and computer scientists are more precise with their terminology than journalists, who write for the layman. In this chapter, I will provide a broad overview of blockchain technology and then explain some of the nuances.
By now, you should understand that there is no such thing as ‘the blockchain,’ just as there is no such thing as ‘the database’ or ‘the network’. ETH is the Ethereum blockchain, a reference to the public Ethereum transaction database—but you can also create private Ethereum blockchains by simply running some node software on some machines and having them connect to each other. Your private Ethereum network will create its own blockchain, and the miners will mine ETH just like in the public network. Your private ETH will not be compatible with the public ETH because your private Ethereum network has a different history from the public version.
In print, if you read ‘the blockchain,’ you may need to make a guess as to what the writer means. In conversation, and at the risk of coming across as pedantic, it should help your understanding to ask early on, ‘Which blockchain platform?’ then, ‘The public chain or a private one?’ As you now know, there are many blockchains, and many variations on how they work.
If you like hierarchies, blockchains fall under the broader category of ‘distributed ledgers’. All blockchains are distributed ledgers, but you can have distributed ledgers that don’t have blocks of data chained together and broadcast to all participants. Sometimes journalists and consultants inaccurately use the term ‘blockchain’ when they are describing non-blockchain distributed ledgers. I guess ‘distributed ledgers’ is too much of a mouthful whereas ‘blockchain’ is a nice memorable buzzword.
We need to differentiate between blockchain technologies and specific blockchain ledgers.
Blockchain technologies are the rules or standards for how a ledger is created and maintained. Different technologies have different rules for participation, different network rules, different specifications for how to create transactions, different methods of storing data, and different consensus mechanisms. When a network is created, the blockchain or ledger of record is initially empty of transactions, just as a new physical leather-bound ledger is empty. Some example blockchain technologies are: Bitcoin, Ethereum, NXT, Corda, Fabric, and Quorum.
Blockchain ledgers themselves are specific instances of ledgers that contain their respective transactions or records.
Think of normal databases. You may have heard of a few types or flavours of databases—Oracle databases, MySQL databases, perhaps others. Each flavour works slightly differently though they are all have similar goals: efficient storage, sorting, and retrieval of data. You can have multiple instances of the same type of database: a company might use more than one Oracle database. And so it is with blockchains. Some blockchain technologies operate one way, others operate a slightly different way and you can have multiple instances of any blockchain technology, in separate ledgers.
Public, Permissionless Blockchains
We’ve explored that cryptocurrencies and some other tokens use public blockchains as their medium of record—that is, their respective transactions are recorded in blocks on a replicated ledger. Public blockchains are also described as permissionless primarily because anyone may create blocks or be a bookkeeper without needing permission from an authority. In these public networks, there is also permissionlessness in another sense—anyone may create an address for receiving funds and create transactions for sending funds.
Private Instances of Public Blockchains
As described earlier, you can run blockchain software on a private network to create a fresh ledger. For example, you could take the Ethereum code and run it, but instead of pointing your node to some computers already running the public Ethereum blockchain, you could point it instead to a few other computers that are not on the public Ethereum network. As far as all of these computers are concerned, they are starting with a fresh ledger with no entries.
Could you set up a small private network running Ethereum, then mine some ETH and transfer them to the public network? No. Although this private network would use the same set of rules as the public blockchain, they have different records of account balances. Nodes on each network can only validate what they see in their own blockchain, and they are not able to see coins on the other blockchain.
Permissioned (or permissionable) blockchains
Some platforms are designed to allow groups of participants to create their own blockchains in a private context. They do not have a global public network. These are called ‘private blockchains’ and they are designed to only allow pre-approved participants to participate. Hence the term ‘permissioned’.
Popular permissioned blockchains include:
•Corda, a platform built from scratch by R3 and a consortium of banks for use by regulated financial institutions but with broad applicability.
•Hyperledger Fabric, a platform built by IBM and donated to the Linux Foundation’s Hyperledger Project. It was originally based heavily on Ethereum but between versions 0.6 and 1.0 was heavily re-architected. Fabric uses a concept of ‘channels’ to restrict parties from seeing all transactions.
•Quorum, a private blockchain system based on Ethereum originally built by JP Morgan. Quorum uses advanced cryptographic constructs called zero knowledge proofs to obfuscate data and address privacy issues.
•Various private instances of Ethereum under development by individual businesses.
Unlike permissionless networks such as Bitcoin and Ethereum, permissioned blockchains don’t need their own native token. They don’t need to incentivise block-creators, and they don’t need proof-of-work as the gating factor to allow participants to write to the shared ledger. Instead, when businesses transact, they are looking for data that can be trusted to be up to date, agreed and signed off by the appropriate parties. In a traditional business ecosystem, participants are all identified, and if some try to misbehave they can be sued. When parties are identified and have legal agreements between them, the technical environment is not as hostile as that of the pseudonymous world of public cryptocurrency blockchains, where code is law and there are no terms of service or legal agreements.
Some cryptocurrency proponents argue that permissioned private blockchains are somehow inferior to public cryptocurrency blockchains. An analogy commonly used is that public cryptocurrency blockchains are like ‘the internet,’ in that they are open, free, and permissionless, whereas private industry blockchains are like intranets, which are closed. The implication here, of course, is that public blockchains will be very successful and disruptive whereas private blockchains are boring, unsuccessful and not very disruptive or game changing200.
Nothing could be further from the truth. Intranets and private company networks are highly successful. I can’t think of any significant company that doesn’t use its own network. And it is equally far from the truth to regard the internet as being open and permissionless. As Tim Swanson notes on his blog in ‘Intranets and the internet’201:
The internet is actually a bunch of private networks of internet service providers (ISPs) that have legal agreements with the end users, cooperate through ‘peering’ agreements with other ISPs, and communicate via a common, standardized routing protocols such as BGP which publishes autonomous system numbers.
The fact is that cryptocurrencies and private blockchains are different tools deployed to address different problems. They are both fine and may happily coexist. In news articles written between 2015 and 2018, blockchain technology was commonly defined as ‘the technology underpinning the cryptocurrency Bitcoin’. This conflates the two ideas and is as enlightening as defining databases as ‘the technology that powers Twitter’.
Public and private blockchains run within different context and ecosystems and, as discussed, are designed to address different problems. So they will naturally operate in different ways. After all, technology is a tool, and tools exist to serve a need. If the needs are different, then it is likely that the tools will be different.
What Is Common to Blockchain Technologies?
Blockchains usually contain the following concepts:
1.A data store (database) that records changes in the data. Up to now they have most commonly been financial transactions, but you can store and record changes to any kind of data in a blockchain.
2.Replication of the data store across a number of systems in real time. ‘Broadcast’ blockchains, such as Bitcoin and Ethereum, ensure that all data is sent to all participants: everyone sees everything. Other technologies are more selective about where data is sent.
3.‘Peer-to-peer’ rather than client-server network architecture. Data may be ‘gossiped’ to neighbours rather than broadcast by a single coordinator acting as the golden source of data.
4.Cryptographic methods such as digital signatures to prove ownership and authenticity, and hashes for references and sometimes to manage write-access.
I often describe blockchain technology as ‘A collection of technologies, a bit like a bag of Legos’. You can take different bricks out of the bag and put them together in different ways to create different results.
Sometimes when discussing specific potential uses for this technology, we hear this exchange:
‘But, you don’t need a blockchain to do that. You can just use traditional technology!’
‘So how would you do it?’
‘Oh, some data storage, some peer-to-peer data sharing, cryptography to ensure authenticity, hashes to ensure data tampering is evident etc’.
‘But you’ve just described how blockchains work!’
So blockchains are not themselves a new invention, but instead, they put together existing technologies to create new capabilities.
What’s the difference between a blockchain and a database?
A common database is a system which simply stores and retrieves data. A blockchain platform is more than that. It stores and retrieves existing data just as a normal database does. It also connects to other peers and listens for new data, validates new data against pre-agreed rules, then stores and broadcasts that new data to other network participants to ensure that they all share the same updated data. And it does so constantly, without manual intervention.
What’s the difference between a distributed database and a distributed ledger?
Replicated databases, where data is copied in real time to multiple machines for resiliency or performance reasons are not new. Sharded databases, where the workload and storage are sharded, or spread around multiple machines, usually to increase speed and storage, are also not new. With distributed ledgers or blockchains, however, participants do not need to trust each other. They do not work on the assumption that the other participants are behaving honestly, so each participant individually checks everything. Richard Brown describes this in his blog202 as a difference in trust boundaries:
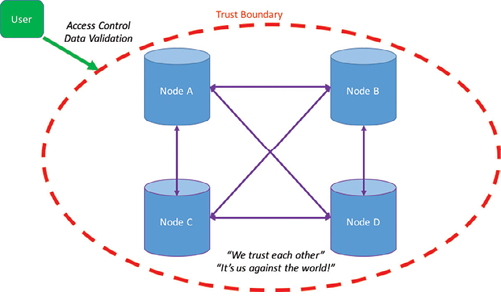
Distributed database
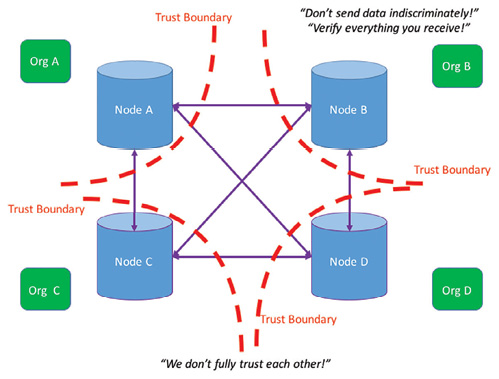
Distributed ledger
What Are Blockchains Good For?
The motivations between public and private blockchains are different. Let’s consider them separately.
To date, public blockchains have been used with some success in the following areas:
1.Speculation
2.Darknet markets
3.Cross border payments
4.Initial Coin Offerings
The main use for cryptocurrencies is undoubtedly speculation. Their prices are volatile and people make and lose a lot of money trading these coins.
The fact that there are no established methods to value a cryptocurrency means that prices are likely to remain volatile for some time. This differs from traditional financial markets where pricing models help to constrain prices to within broadly understood limits. Equities have well-established pricing methodologies. Discounted forecast cashflows, book value, and enterprise value calculations can help to establish a consensus on the value of a company. Ratios such as earnings per share, price to earnings, and return on assets can help to compare share prices between similar companies. Fiat currencies trade on the basis of comparative economic data. Other traditional financial assets have other standardised pricing methodologies. Up to now, however, I have not seen credible methods for pricing cryptocurrencies or ICO tokens. This is changing—as the industry matures, pricing models are being explored, but it will take some time for these models to become widely accepted.
Cryptocurrencies have been used with some success to buy items from underground marketplaces.
Unfortunately for some, the traceability of certain cryptocurrencies makes them flawed candidates for illegal activity. In 2015, two US Federal Agents from the Drug Enforcement Agency (DEA) and the US Secret Service, sought to enrich themselves while conducting an undercover investigation of the Silk Road drug marketplace. Perhaps they believed that Bitcoin was anonymous and untraceable. They allegedly stole, bribed, blackmailed, and laundered the proceeds while under cover and were eventually charged with money laundering and wire fraud. Here is an excerpt from a press release issued by the US Department of Justice203:
Carl M. Force, 46, of Baltimore, was a Special Agent with the DEA, and Shaun W. Bridges, 32, of Laurel, Maryland, was a Special Agent with the U.S. Secret Service (USSS). Both were assigned to the Baltimore Silk Road Task Force, which investigated illegal activity in the Silk Road marketplace. Force served as an undercover agent and was tasked with establishing communications with a target of the investigation, Ross Ulbricht, a.k.a. ‘Dread Pirate Roberts’. Force is charged with wire fraud, theft of government property, money laundering and conflict of interest. Bridges is charged with wire fraud and money laundering.
According to the complaint, Force was a DEA agent assigned to investigate the Silk Road marketplace. During the investigation, Force engaged in certain authorized undercover operations by, among other things, communicating online with ‘Dread Pirate Roberts’ (Ulbricht), the target of his investigation. The complaint alleges, however, that Force then, without authority, developed additional online personas and engaged in a broad range of illegal activities calculated to bring him personal financial gain. In doing so, the complaint alleges, Force used fake online personas, and engaged in complex Bitcoin transactions to steal from the government and the targets of the investigation. Specifically, Force allegedly solicited and received digital currency as part of the investigation, but failed to report his receipt of the funds, and instead transferred the currency to his personal account. In one such transaction, Force allegedly sold information about the government’s investigation to the target of the investigation. The complaint also alleges that Force invested in and worked for a digital currency exchange company while still working for the DEA, and that he directed the company to freeze a customer’s account with no legal basis to do so, then transferred the customer’s funds to his personal account. Further, Force allegedly sent an unauthorized Justice Department subpoena to an online payment service directing that it unfreeze his personal account.
Bridges allegedly diverted to his personal account over $800,000 in digital currency that he gained control of during the Silk Road investigation. The complaint alleges that Bridges placed the assets into an account at Mt. Gox, the now-defunct digital currency exchange in Japan. He then allegedly wired funds into one of his personal investment accounts in the United States mere days before he sought a $2.1 million seizure warrant for Mt. Gox’s accounts.
On 1 July 2015, Force pled guilty to money laundering with predicates of wire fraud and theft of government property, obstruction of justice, and extortion. Later, on 31 August 2015, Bridges admitted that he stole over $800,000 of Bitcoin while on the case, and pled guilty to money laundering and obstruction of justice204
What can we learn from this? Don’t use bitcoins to perform or fund illegal activities.
While there may have been some limited success in using cryptocurrencies as a vehicle to move fiat across borders, adoption has been limited. I personally performed an experiment in 2014 when I sent $200 Singapore dollars to my friend in Indonesia205 using three methods: Western Union, bank transfer, and Bitcoin. The Bitcoin route was by far the worst user experience, and the most expensive. However, Bitcoin has become more usable since then, and I expect it to continue to improve further.
The core problem is that in a conventional fiat-to-fiat remittance, whether through a financial services agency such as Western Union or through the banking system, there is only one exchange of currencies. Using cryptocurrencies, there are now two exchanges: fiat to crypto, then crypto to fiat. More exchanges mean more steps, complexity, and cost.
Cross border payments were initially trumpeted as a ‘killer app’ for Bitcoin and cryptocurrencies, especially in 2014–15, but in 2018 there is less media attention for this particular use of cryptocurrency. Indeed, in June 2018, money transfer agency Western Union announced that they had been testing XRP for six months and were yet to see any savings206. Perhaps the industry is in the ‘trough of disillusionment’ in Gartner’s technology hype cycle207.
ICOs are a new method of fundraising that became popular in 2016. Companies offer tokens to people in return for cryptocurrency. Tokens usually represent a claim on future goods or services provided by that company. We discuss ICOs in more detail in the next section.
Some merchants use cryptocurrency payment processors to accept cryptocurrencies from customers as payment. In 2014 and 2015, it was a cheap way for merchants to get press releases and seem innovative. However, since then many have quietly removed this payment mechanism due to lack of customer interest.
I have seen public blockchains being used for other ‘fringe’ purposes, for example the storing of hashes on a blockchain to prove that some data existed at a certain point in time. I haven’t seen evidence that this use is particularly widespread.
Critics of cryptocurrencies often claim that they are widely used for money laundering. While there is undoubtedly some laundering of illicit funds using cryptocurrencies, as there is using fiat currencies, it is hard to tell at this stage what proportion of cryptocurrency transactions are used for this purpose, and what proportion of global money laundering is performed through cryptocurrencies. For serious organised crime, I suspect that the cryptocurrency markets are just too small and illiquid to satisfy their demands. Big business enterprises, high value banknotes, even banks still are more likely to be the preferred vehicles for most money laundering.
While public blockchains have enabled censorship resistant digital cash, they were not designed to solve problems that traditional businesses have. What are the challenges within existing businesses, and how might concepts borrowed from public blockchains help improve how they operate?
Business-to-business communication
Processes within an organisation have, over time, been made efficient by use of internal systems, workflow tools, intranets, and data repositories. However, the sophistication of technology used to communicate between organisations has remained low. In some advanced situations, APIs (application programming interfaces) are used for machine to machine communications, but in the majority of cases we rely on emails and pdf files. It is still common for pieces of paper with wet-ink signatures to be couriered across the world.
Duplicative data, processes, and reconciliation
Businesses trust their own data but not anyone else’s. This means that businesses within an ecosystem duplicate data and processes. Digital files and records are often replicated within and between multiple organisations, with none of them being the golden source. Version control of documents and records is painful unless a third party is paid to be the golden source. Reconciliation only goes some way to solve these pain points.
Consider a digital invoice issued by company A to company B. The invoice could be a pdf file which is created by someone at company A, perhaps signed off by someone else in company A before a copy is sent from the accounts receivable department to someone at company B. Someone at company B receives it in their inbox, saves a copy on their hard drive, and forwards a copy to someone else, perhaps their manager, to sign off. Another copy goes to the accounts payable department and, when the invoice is paid, everyone needs to be updated. There could be ten or more copies of the same asset—the invoice—floating around various computers, none of which are kept in sync. When the state of the invoice changes from ‘unpaid’ to ‘paid,’ this is not reflected on all of the copies of the invoice.
Private blockchains
So it is not surprising that businesses have become interested in concepts popularised by public blockchains such as unique digital assets, trusted automation, and cryptographically secured ledger entries. However, the radical transparency of public blockchains is not attractive to businesses that quite legitimately may require a level of commercial confidentiality.
Private blockchains have been inspired by public blockchains but are being designed to meet the needs of business. They adopt some concepts from public blockchains and reject others. By relaxing the strict requirements of public blockchains around permissionlessness and censorship resistance, private blockchains do not need mechanisms such as the energy-intensive proof-of-work mining.
Some technology inspired by public blockchains do not have blocks in chains at all! They are sometimes more accurately called ‘distributed ledgers’. Corda, a distributed ledger platform built by R3 and a group of banks, is an open source platform that uses many of the concepts from public blockchains, but it doesn’t bundle transactions up into blocks for batch processing and distribution across the whole network. This addresses some privacy concerns as only the businesses who are involved in a transaction see it.
A key benefit of blockchains and other similar data structures that use chains of hashes is that parties have the ability to know for themselves that a set of statements is complete (not missing any) and that the statements themselves are complete and untampered. Each party can verify this for themselves without having to check with another party. This is useful in many business situations, not least banks who need to know that their list of trades is complete and the data within the trades is consistent with their counterparty.
Private blockchains aim to increase the quality and security of technology used in business-to-business communications. They allow unique digital assets to move freely and reliably between companies without the need to have a third party act as a record keeper. Private blockchains can provide transparent multilateral workflows in the form of smart contracts, and demonstrate that the agreed workflows are adhered to. This is what is meant by ‘trustless automation’. Instead of having to trust a business to perform as agreed, a smart contract ensures that pre-programmed processes are followed.
Private blockchains may be useful any time a business interacts with another business to share workflows, processes, or assets. When does this happen? Pretty much all of the time! Most businesses don’t operate in a vacuum; they need to interact with other businesses. The financial services industry was the first to invest, to understand, and to use this technology, specifically for wholesale banking and in financial markets. This makes sense, as the industry is dominated by business-to-business workflows, intermediaries, and digital assets; and the ‘back office’ had not received significant investment in decades. Perhaps the fact that Bitcoin was described as a cryptocurrency also made it interesting to banks.
Let’s revisit the invoice example. Imagine now if the invoice was recorded on some sort of ledger that was kept in sync between both companies, bilaterally, and as soon as it was approved, signed, or paid, both parties would know about it. This could streamline many business processes, and the concepts could be extended to any document, record, or data.
Of course, many business-to-business workflows could be digitised and automated if you could find a party to store the data and be the golden source. In some cases, they are. SWIFT and Bolero are examples that fit this category. But in other cases, a third party may not be viable, either because everyone wants to be it or no one wants to be it, or there are regulatory or geographical reasons preventing the emergence of such a party. Industries can be suspicious of single points of power and control, and wary of the monopolistic behaviour that often emerges from this. Central repositories of data could have competitive implications if leaked or misused. So there are a number of reasons why an apparently obvious solution of having a third party may not be viable.
Non-financial industries are now becoming interested in exploring the technology for, among other things, digital identity, supply chains, trade finance, healthcare, procurement, real estate, and asset registries.
Some private or permissioned blockchains are certainly gaining mindshare and traction. Current examples are:
Axoni AxCore
Axoni is a capital market technology firm founded in 2013 that specialises in distributed ledger technology and blockchain infrastructure. Among other projects, Axoni’s flagship initiative is use of their technology to upgrade the Depository Trust & Clearing Corporation’s trade information warehouse208.
R3 Corda
Corda is an open source blockchain project designed to solve pain points in the financial services industry. It was designed by a consortium of banks and R3, my employer, so I declare my interest here. In Chief Technology Officer Richard Brown’s own words209:
Corda is an open source enterprise blockchain platform that has been designed and built from the ground up to enable legal contracts and other shared data to be managed and synchronised between mutually untrusting organisations in any industry. Uniquely amongst enterprise blockchain platforms, Corda allows a diverse range of applications to interoperate on a single global network.
Corda uses concepts drawn from Bitcoin and public blockchains to guarantee that digital assets are unique and data is synchronised between databases controlled by different parties, though it diverges from other blockchains in that it does not bundle unrelated transactions together and distribute them to all participants in a network for periodic processing. This means it can process higher transaction volumes and resolves the privacy issue of public blockchains. Although Corda was originally designed for regulated financial institutions, it is now being actively explored by other industries.
Corda is being used, among other things, for trading baskets of financial assets210, for gold trading211, syndicated loans212, and FX trade matching213.
Digital Asset GSL
Digital Asset Holdings, LLC is a company founded in 2014. According to Wikipedia214, it ‘Builds products based on distributed ledger technology (DLT) for regulated financial institutions, such as financial market infrastructure providers, CCPs, CSDs, exchanges, banks, custodians and their market participants’. The technology platform is called the Global Synchronization Log (GSL).
Digital Asset has a notable contract to use DLT to modernise and replace the Australian Stock Exchange’s technology systems215. This is regarded as a major vote of confidence for Digital Asset and the entire private blockchain industry.
Hyperledger Fabric
Hyperledger Fabric is a blockchain technology originally developed by IBM and Digital Asset, and incubated under the Linux Foundation’s Hyperledger Project. It seems to have some traction in supply chains and healthcare.
JP Morgan Quorum
Quorum is a blockchain technology originally created by US bank JP Morgan Chase and is based on the Ethereum platform. It is interesting because it uses advanced cryptographic techniques called zero knowledge proofs to obfuscate transaction data. In March 2018, the Financial Times reported that JP Morgan was considering spinning off the project into its own entity216.
Many experiments using blockchain technology have been announced by startups and incumbents alike. Thy are often described as ‘use-cases,’ a term that implies, optimistically, that a blockchain would be a good use for the particular problem described. This selection of experiments collated by Peter Bergstrom217 gives a flavour of the scope of interest in blockchain use:

And here are is a beautiful infographic from Matteo Gianpietro Zago218:
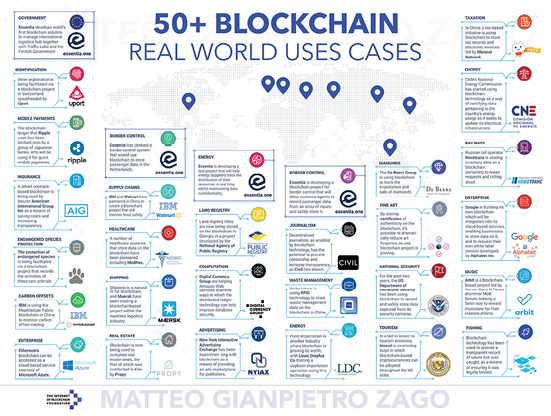
I include these lists as examples of the sharable but ultimately misleading hype that is propagated in the mainstream and social media. These are not actual use cases. They are experiments to apply blockchain technology to a variety of industries and business workflows, appropriately or not.

Use case for a computer: Door stop
Just as you could draft a letter using spreadsheet software, you can use a blockchain in almost any business situation that involves data. After all, a blockchain is a database with some additional features. In my view, many of these experiments will not deliver the promised benefits because more appropriate software and tools are available. However, some may succeed or evolve and get traction.
It is still unclear which processes will be significantly improved as a direct consequence of the technology, and which are improved simply by digitising the workflows.
Does it matter? In many cases a project might not need a blockchain, but using one might trigger interest and management enthusiasm, and even unlock a budget which might not have been available if the project was just a boring old digitisation project. This is fine, and in this case, I think the ends justify the means. Without some amount of hype to spark the imagination there would be less money to spend on innovating, and therefore potentially less innovation.
With so many attempts to use blockchain technology, how do you attempt to understand the use and value of blockchain technology in these experiments?
There are certain questions that can be useful to ask. Earlier we asked, ‘Which blockchain?’ and, ‘The public one or a private one?’ From there, the questions depend on the answers to the original questions. Here are a few to get started.
For public blockchains, it is useful to understand:
•Will all parties run nodes or will some trust others?
•If the blockchain is backlogged, what impact might have this have on users?
•How will the project deal with forks and chainsplits?
•How will data privacy be achieved?
•How will operators comply with evolving regulations?
For private blockchains, it is useful to understand:
•Who will run the nodes? Why?
•Who is going to write blocks?
•Who is going to validate blocks and why?
•If this is about data sharing, why can’t a web server be used?
•Is there a natural central authority whom everyone trusts, and if so why aren’t they hosting a portal?
For any type of blockchain:
•What data is represented on the blockchain and what data is ‘off-chain?’
•What do the tokens represent?
•When a token is passed from one party to another what does this mean in real life?
•What happens if a private key is lost or copied? Is this acceptable?
•Are all parties comfortable with the data that is being passed around the network?
•How will upgrades be managed?
•What’s in the blocks?!219
Depending on the project, some of these questions may be more relevant than others. Some of the solutions may come from network-wide innovations. For example, public chains can currently become congested but innovations such as payment channels may enable much higher throughput. There are many more questions to ask, depending on the project.
The point is that you should not take the breathless media announcements at face value, but take a more investigative approach to uncover if there is value in these experiments or not. At this stage of the innovation cycle, an honest ‘I don’t know’ is an acceptable answer for some of these questions, and it is more important to understand the trade-offs than to immediately pass judgment on the solutions.